The threat actors associated with the Gootkit malware have made “notable changes” to their toolset, adding new components and obfuscations to their infection chains.
Google-owned Mandiant is monitoring the activity cluster under the moniker UNC2565, noting that the usage of the malware is “exclusive to this group.”
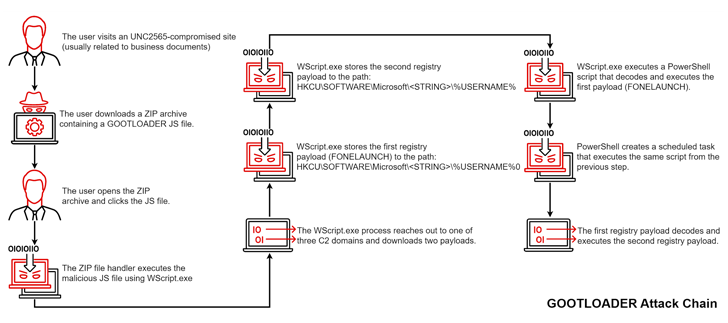
Gootkit, also called Gootloader, is spread through compromised websites that victims are tricked into visiting when searching for business-related documents like agreements and contracts via a technique called search engine optimization (SEO) poisoning.
The purported documents take the form of ZIP archives that harbor the JavaScript malware, which, when launched, paves the way for additional payloads such as Cobalt Strike Beacon, FONELAUNCH, and SNOWCONE.
FONELAUNCH is a .NET-based loader designed to load an encoded payload into memory, and SNOWCONE is a downloader that’s tasked with retrieving next-stage payloads, typically IcedID, via HTTP.
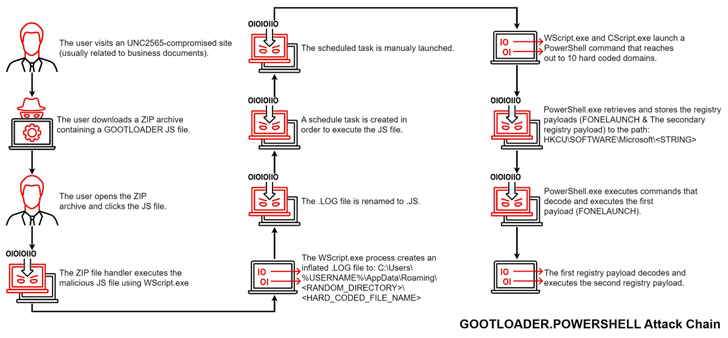
While the overarching goals of Gootkit have remained unchanged, the attack sequence in itself has received significant updates, wherein the JavaScript file within the ZIP archive is trojanized and contains another obfuscated JavaScript file that consequently proceeds to execute the malware.
The new variant, which was spotted by the threat intelligence firm in November 2022, is being tracked as GOOTLOADER.POWERSHELL. It’s worth noting that the revamped infection chain was also documented by Trend Micro earlier this month, detailing Gootkit attacks targeting the Australian healthcare sector.
What’s more, the malware authors are said to have taken three different approaches to obscure Gootkit, including concealing the code within altered versions of legitimate JavaScript libraries such as jQuery, Chroma.js, and Underscore.js, in an attempt to escape detection.
It’s not just Gootkit, as three different flavors of FONELAUNCH – FONELAUNCH.FAX, FONELAUNCH.PHONE, and FONELAUNCH.DIALTONE – have been put to use by UNC2565 since May 2021 to execute DLLs, .NET binaries, and PE files, indicating that the malware arsenal is being continuously maintained and updated.
“These changes are illustrative of UNC2565’s active development and growth in capabilities,” Mandiant researchers Govand Sinjari and Andy Morales said.