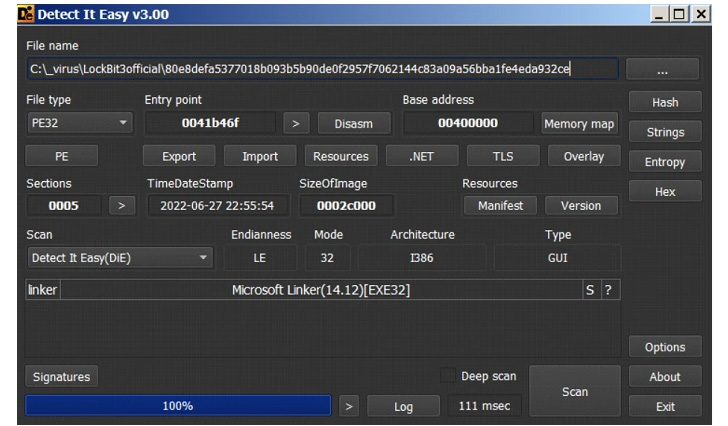
Cybersecurity researchers have reiterated similarities between the latest iteration of the LockBit ransomware and BlackMatter, a rebranded variant of the DarkSide ransomware strain that closed shop in November 2021.
The new version of LockBit, called LockBit 3.0 aka LockBit Black, was released in June 2022, launching a brand new leak site and what’s the very first ransomware bug bounty program, alongside Zcash as a cryptocurrency payment option.
Its encryption process involves appending the extension “HLJkNskOq” or “19MqZqZ0s” to each and every file and changing the icons of the locked files to that of the .ico file that’s dropped by the LockBit sample to kick-start the infection.
“The ransomware then drops its ransom note, which references ‘Ilon Musk’ and the European Union’s General Data Protection Regulation (GDPR),” Trend Micro researchers said in a Monday report. “Lastly, it changes the wallpaper of the victim’s machine to inform them of the ransomware attack.”
LockBit’s extensive similarities to BlackMatter come from overlaps in the privilege escalation and harvesting routines used to identify APIs required to terminate processes and other functions as well as the use of anti-debugging and threading techniques designed to thwart analysis.
Also of note is its use of a “-pass” argument to decrypt its main routine, a behavior seen in another defunct ransomware family named Egregor, effectively making the binary harder to reverse if the parameter is not available.
In addition, LockBit 3.0 is designed to check the victim machine’s display language to avoid compromising systems associated with the Commonwealth of Independent States (CIS) states.
“One notable behavior for this third LockBit version is its file deletion technique: Instead of using cmd.exe to execute a batch file or command that will perform the deletion, it drops and executes a .tmp file decrypted from the binary,” the researchers said.
This .tmp file then overwrites the contents of the ransomware binary and then renames the binary several times, with the new file names based on the length of the original file name, including the extension, in an attempt to prevent recovery by forensic tools and cover its tracks.
The findings come as LockBit infections have emerged as the most active ransomware-as-a-service (RaaS) groups in 2022, the most recent allegedly being the Italian Internal Revenue Service (L’Agenzia delle Entrate).
According to Palo Alto Networks 2022 Unit 42 Incident Response Report published today based on 600 cases handled between May 2021 and April 2022, the ransomware family accounted for 14% of the intrusions, second only to Conti at 22%.
The development also highlights the continued success of the RaaS business model, lowering the barrier to entry for extortionists and expanding the reach of ransomware.
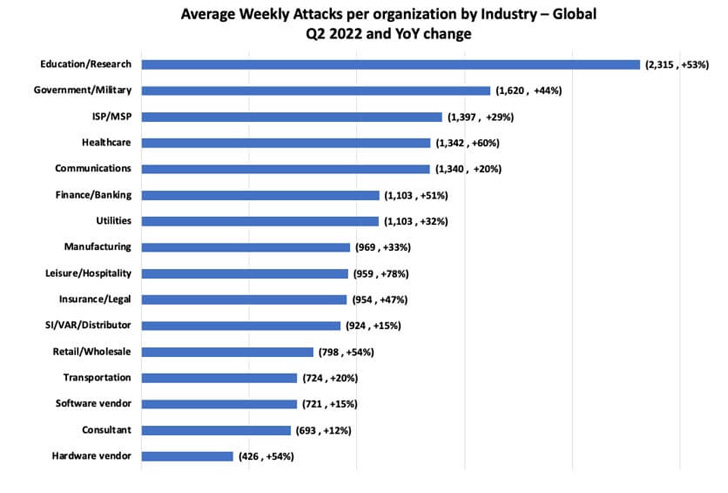
Check Point’s analysis of cyberattack trends for Q2 2022 shows that the weekly average of impacted organizations by ransomware reached one out of 40, a 59% increase YoY from one out of 64 organizations in Q2 2021.
“Latin America has seen the largest increase in attacks, spotting one out of 23 organizations impacted weekly, a 43% increase YoY, compared to one out of 33 in Q2 2021, followed by Asia region that has seen a 33% increase YoY, reaching one out of 17 organizations impacted weekly,” the Israeli cybersecurity firm said.