In a new joint cybersecurity advisory, U.S. cybersecurity and intelligence agencies have warned about the use of Maui ransomware by North Korean government-backed hackers to target the healthcare sector since at least May 2021.
“North Korean state-sponsored cyber actors used Maui ransomware in these incidents to encrypt servers responsible for healthcare services—including electronic health records services, diagnostics services, imaging services, and intranet services,” the authorities noted.
The alert comes courtesy of the U.S. Cybersecurity and Infrastructure Security Agency (CISA), the Federal Bureau of Investigation (FBI), and the Department of the Treasury.
Cybersecurity firm Stairwell, whose findings formed the basis of the advisory, said the lesser-known ransomware family stands out because of a lack of several key features commonly associated with ransomware-as-a-service (RaaS) groups.
This includes the absence of “embedded ransom note to provide recovery instructions or automated means of transmitting encryption keys to attackers,” security researcher Silas Cutler said in a technical overview of the ransomware.
Instead, analysis of Maui samples suggests that the malware is designed for manual execution by a remote actor via a command-line interface, using it to target specific files on the infected machine for encryption.
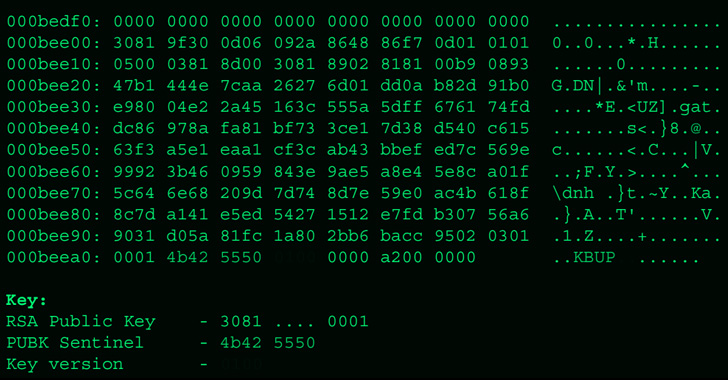
Besides encrypting target files with AES 128-bit encryption with a unique key, each of these keys is, in turn, encrypted with RSA using a key pair generated the first time when Maui is executed. As a third layer of security, the RSA keys are encrypted using a hard-coded RSA public key that’s unique to each campaign.
What sets Maui apart from other traditional ransomware offerings is also the fact that it’s not offered as a service to other affiliates for use in return for a share of monetary profits.
In some instances, the ransomware incidents are said to have disrupted health services for extended periods of time. The initial infection vector used to conduct the intrusions is unknown as yet.
It’s worth noting that the campaign is predicated on the willingness of healthcare entities to pay ransoms to quickly recover from an attack and ensure uninterrupted access to critical services. It’s the latest indication of how North Korean adversaries are adapting their tactics to illegally generate a constant stream of revenue for the cash-strapped nation.
According to the Sophos’ State of Ransomware in Healthcare 2022 report, 61% of healthcare organizations surveyed opted to settle compared with the global average of 46%, with only 2% of those that paid the ransom in 2021 getting their complete data back.
That said, the use of a manually operated ransomware family by an APT group also raises the possibility that the operation could be a diversionary tactic designed to act as a cover for other malicious motives, as recently observed in the case of Bronze Starlight.
“Nation state-sponsored ransomware attacks have become typical international acts of aggression,” Peter Martini, co-founder of iboss, said in a statement. “Unfortunately, North Korea specifically has shown it is very willing to indiscriminately target various industries, including healthcare, to secure untraceable cryptocurrency that is funding its nuclear weapons program.”