An enterprise-grade surveillanceware dubbed Hermit has been put to use by entities operating from within Kazakhstan, Syria, and Italy over the years since 2019, new research has revealed.
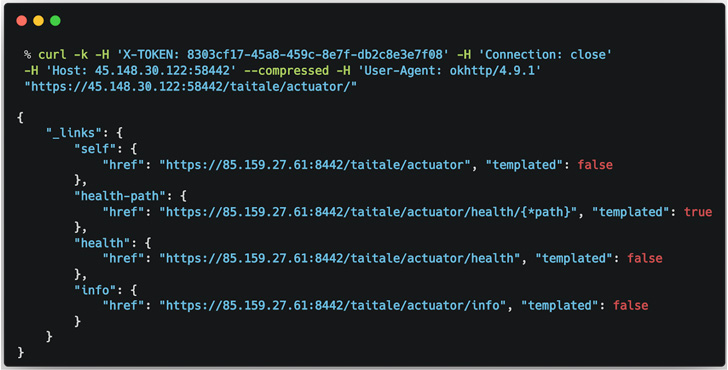
Lookout attributed the spy software, which is equipped to target both Android and iOS, to an Italian company named RCS Lab S.p.A and Tykelab Srl, a telecom services provider which it suspects to be a front company. The San Francisco-based cybersecurity firm said it detected the campaign aimed at Kazakhstan in April 2022.
Hermit is modular and comes with myriad capabilities that allow it to “exploit a rooted device, record audio and make and redirect phone calls, as well as collect data such as call logs, contacts, photos, device location and SMS messages,” Lookout researchers Justin Albrecht and Paul Shunk said in a new write-up.
The spyware is believed to be distributed via SMS messages that trick users into installing what are seemingly innocuous apps from Samsung, Vivo, and Oppo, which, when opened, loads a website from the impersonated company while stealthily activating the kill chain in the background.
Like other Android malware threats, Hermit is engineered to abuse its access to accessibility services and other core components of the operating system (i.e., contacts, camera, calendar, clipboard, etc.) for most of its malicious activities.
Android devices have been at the receiving end of spyware in the past. In November 2021, the threat actor tracked as APT-C-23 (aka Arid Viper) was linked to a wave of attacks targeting Middle East users with new variants of FrozenCell.
Then last month, Google’s Threat Analysis Group (TAG) disclosed that at least government-backed actors located in Egypt, Armenia, Greece, Madagascar, Côte d’Ivoire, Serbia, Spain, and Indonesia are buying Android zero-day exploits for covert surveillance campaigns.
“RCS Lab, a known developer that has been active for over three decades, operates in the same market as Pegasus developer NSO Group Technologies and Gamma Group, which created FinFisher,” the researchers noted.
“Collectively branded as ‘lawful intercept’ companies, they claim to only sell to customers with legitimate use for surveillanceware, such as intelligence and law enforcement agencies. In reality, such tools have often been abused under the guise of national security to spy on business executives, human rights activists, journalists, academics and government officials.”
The findings come as the Israel-based NSO Group is said to be reportedly in talks to sell off its Pegasus technology to U.S. defense contractor L3Harris, the company that manufactures StingRay cellular phone trackers, prompting concerns that it could open the door for law enforcement’s use of the controversial hacking tool.
The German maker behind FinFisher has been courting troubles of its own in the wake of raids conducted by investigating authorities in connection with suspected violations of foreign trading laws by way of selling its spyware in Turkey without obtaining the required license.
Earlier this March, it shut down its operations and filed for insolvency, Netzpolitik and Bloomberg reported, adding, “the office has been dissolved, the employees have been laid off, and business operations have ceased.”