Telecom company T-Mobile on Friday confirmed that it was the victim of a security breach in March after the LAPSUS$ mercenary gang managed to gain access to its networks.
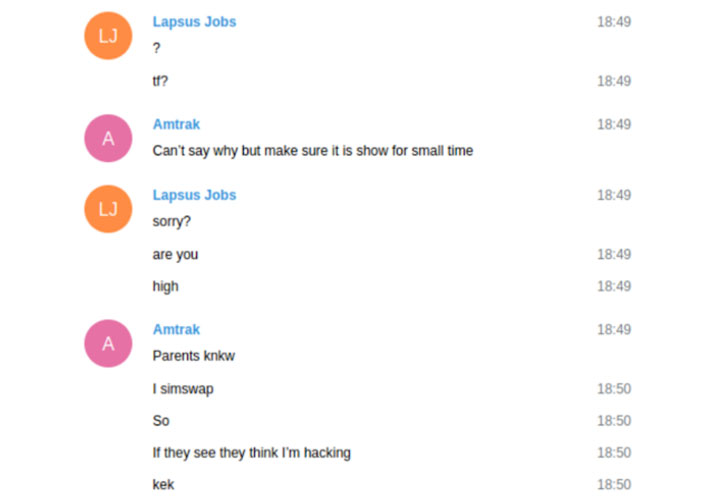
The acknowledgment came after investigative journalist Brian Krebs shared internal chats belonging to the core members of the group indicating that LAPSUS$ breached the company several times in March prior to the arrest of its seven members.
T-Mobile, in a statement, said that the incident occurred “several weeks ago, with the “bad actor” using stolen credentials to access internal systems. “The systems accessed contained no customer or government information or other similarly sensitive information, and we have no evidence that the intruder was able to obtain anything of value,” it added.
The VPN credentials for initial access are said to have been obtained from illicit websites like Russian Market with the goal of gaining control of T-Mobile employee accounts, ultimately allowing the threat actor to carry out SIM swapping attacks at will.
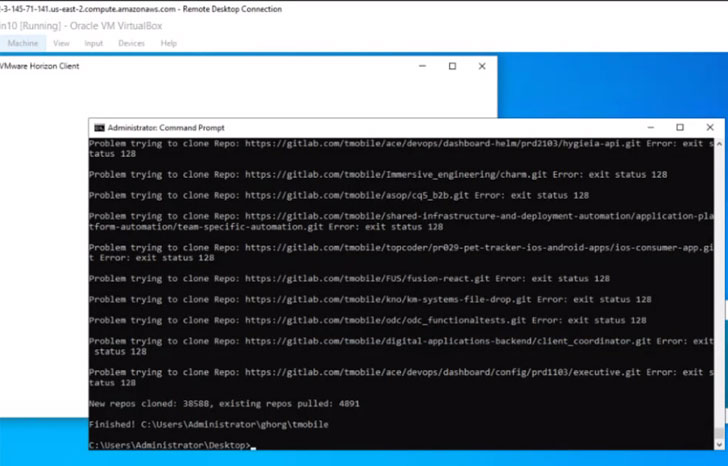
Besides gaining access to an internal customer account management tool called Atlas, the chats show that LAPSUS$ had breached T-Mobile’s Slack and Bitbucket accounts, using the latter to download over 30,000 source code repositories.
LAPSUS$, in a short time since emerging on the threat landscape, have gained notoriety for its breaches of Impresa, NVIDIA, Samsung, Vodafone, Ubisoft, Microsoft, Okta, and Globant.
Earlier this month, the City of London Police disclosed that it had charged two of the seven teenagers, a 16-year-old and a 17-year-old, who were arrested last month for their alleged connections to the LAPSUS$ data extortion gang.