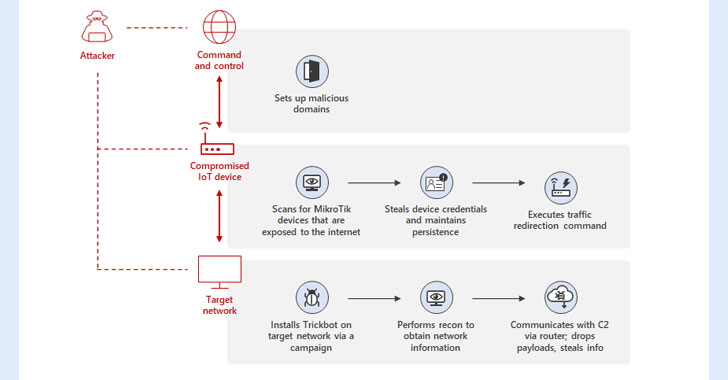
Microsoft on Wednesday detailed a previously undiscovered technique put to use by the TrickBot malware that involves using compromised Internet of Things (IoT) devices as a go-between for establishing communications with the command-and-control (C2) servers.
“By using MikroTik routers as proxy servers for its C2 servers and redirecting the traffic through non-standard ports, TrickBot adds another persistence layer that helps malicious IPs evade detection by standard security systems,” Microsoft’s Defender for IoT Research Team and Threat Intelligence Center (MSTIC) said.
TrickBot, which emerged as a banking trojan in 2016, has evolved into a sophisticated and persistent threat, with its modular architecture enabling it to adapt its tactics to suit different networks, environments, and devices as well as offer access-as-a-service for next-stage payloads like Conti ransomware.
The expansion to TrickBot’s capabilities comes amid reports of its infrastructure going offline, even as the botnet has continually refined its features to make its attack framework durable, evade reverse engineering, and maintain the stability of its C2 servers.
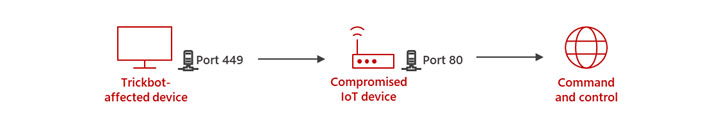
Specifically, the new method identified by MSTIC involves leveraging hacked IoT devices such as routers from MikroTik to “create a line of communication between the TrickBot-affected device and the C2 server.”
This also entails breaking into the routers by using a combination of methods, namely default passwords, brute-force attacks, or exploiting a now-patched flaw in MikroTik RouterOS (CVE-2018-14847), followed by changing the router’s password to maintain access.
In the next step, the attackers then issue a network address translation (NAT) command that’s designed to redirect traffic between ports 449 and 80 in the router, establishing a path for the TrickBot-infected hosts to communicate with the C2 server.
“As security solutions for conventional computing devices continue to evolve and improve, attackers will explore alternative ways to compromise target networks,” the researchers said. “Attack attempts against routers and other IoT devices are not new, and being unmanaged, they can easily be the weakest links in the network.”