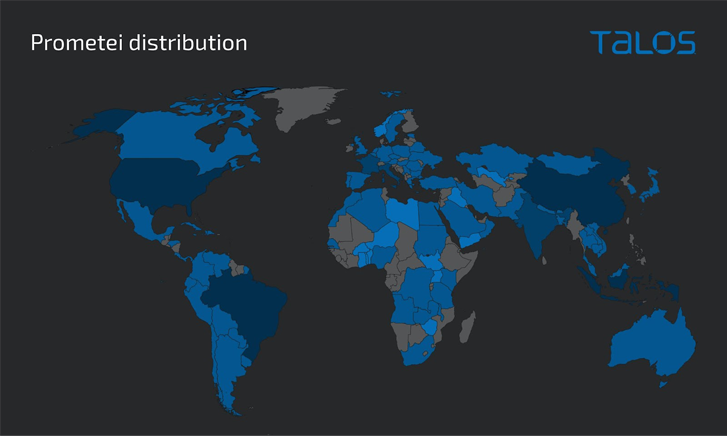
An updated version of a botnet malware called Prometei has infected more than 10,000 systems worldwide since November 2022.
The infections are both geographically indiscriminate and opportunistic, with a majority of the victims reported in Brazil, Indonesia, and Turkey.
Prometei, first observed in 2016, is a modular botnet that features a large repertoire of components and several proliferation methods, some of which also include the exploitation of ProxyLogon Microsoft Exchange Server flaws.
It’s also notable for avoiding striking Russia, suggesting that the threat actors behind the operation are likely based in the country.
The cross-platform botnet’s motivations are financial, primarily leveraging its pool of infected hosts to mine cryptocurrency and harvest credentials.
The latest variant of Prometei (called v3) improves upon its existing features to challenge forensic analysis and further burrow its access on victim machines, Cisco Talos said in a report shared with The Hacker News.
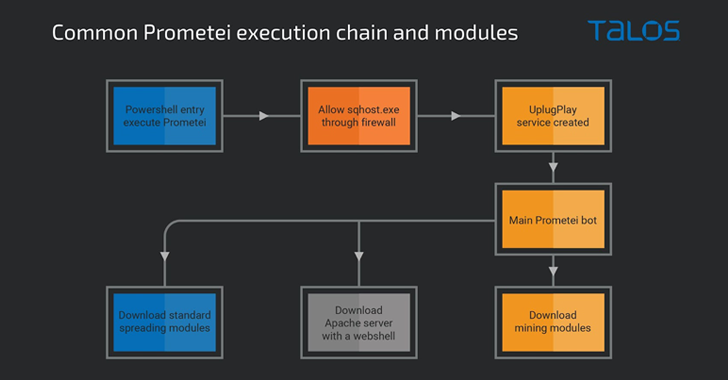
The attack sequence proceeds thus: Upon gaining a successful foothold, a PowerShell command is executed to download the botnet payload from a remote server. Prometei’s main module is then used to retrieve the actual crypto-mining payload and other auxiliary components on the system.
Some of these support modules function as spreader programs designed to propagate the malware through Remote Desktop Protocol (RDP), Secure Shell (SSH), and Server Message Block (SMB).
Discover the Hidden Dangers of Third-Party SaaS Apps
Are you aware of the risks associated with third-party app access to your company’s SaaS apps? Join our webinar to learn about the types of permissions being granted and how to minimize risk.
Prometei v3 is also noteworthy for using a domain generation algorithm (DGA) to build out its command-and-control (C2) infrastructure. It further packs in a self-update mechanism and an expanded set of commands to harvest sensitive data and commandeer the host.
Last but not least, the malware deploys an Apache web server that’s bundled with a PHP-based web shell, which is capable of executing Base64-encoded commands and carrying out file uploads.
“This recent addition of new capabilities [indicates] that the Prometei operators are continuously updating the botnet and adding functionality,” Talos researchers Andrew Windsor and Vanja Svajcer said.