A previously unknown threat actor dubbed NewsPenguin has been linked to a phishing campaign targeting Pakistani entities by leveraging the upcoming international maritime expo as a lure.
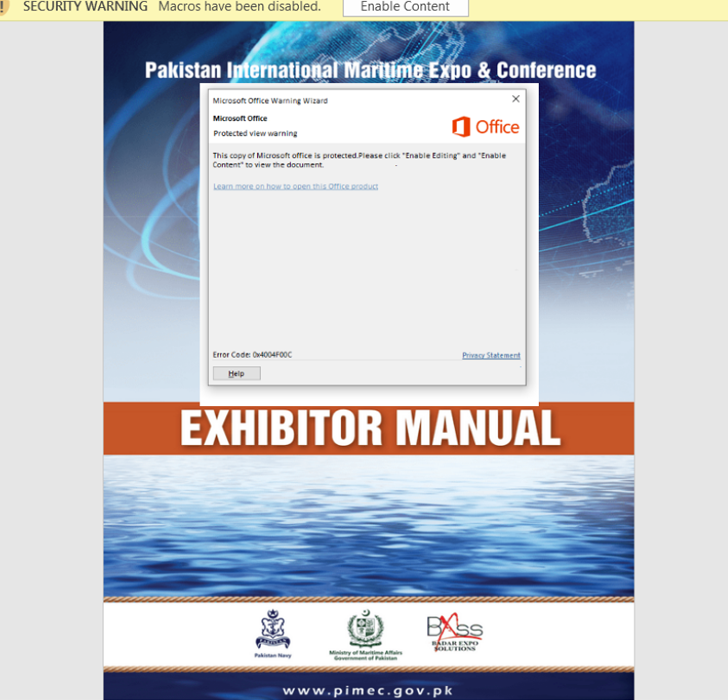
“The attacker sent out targeted phishing emails with a weaponized document attached that purports to be an exhibitor manual for PIMEC-23,” the BlackBerry Research and Intelligence Team said.
PIMEC, short for Pakistan International Maritime Expo and Conference, is an initiative of the Pakistan Navy and is organized by the Ministry of Maritime Affairs with an aim to “jump start development in the maritime sector.” It’s scheduled to be held from February 10-12, 2023.
The Canadian cybersecurity company said the attacks are designed to target marine-related entities and the event’s visitors by tricking the message recipients into opening the seemingly harmless Microsoft Word document.
Once the document is launched, a method called remote template injection is employed to fetch the next-stage payload from an actor-controlled server that’s configured to return the artifact only if the request is sent from an IP address located in Pakistan.
BlackBerry said it found the server to be hosting two ZIP archive files sans any password protections, one of which includes a Windows executable (updates.exe) that functions as a covert spying tool capable of bypassing sandboxes and virtual machines.
What’s more, the contents of the binary are encrypted with the XOR encryption algorithm, where the XOR key is “penguin.” The HTTP response containing the backdoor also comes with the name parameter in the Content-Disposition response header set to “getlatestnews.”
The name NewsPenguin is a reference to the uncommon XOR key and the name parameter, with BlackBerry finding no tactical overlaps that connect the malware to any currently-known threat actor or group.
An analysis of the domain hosting the payloads shows that it has been registered since June 30, 2022, indicating some level of advance planning for the campaign while simultaneously taking steps to iterate its toolset.
“As the target is an event run by the Pakistan Navy, it implies that the threat actor is actively targeting government organizations, rather than this being a financially motivated attack,” BlackBerry said.