Researchers have shed light on a new hybrid malware campaign targeting both Android and Windows operating systems in a bid to expand its pool of victims.
The attacks entail the use of different malware such as ERMAC, Erbium, Aurora, and Laplas, according to a ThreatFabric report shared with The Hacker News.
“This campaign resulted in thousands of victims,” the Dutch cybersecurity company said, adding, “Erbium stealer successfully exfiltrated data from more then 1,300 victims.”
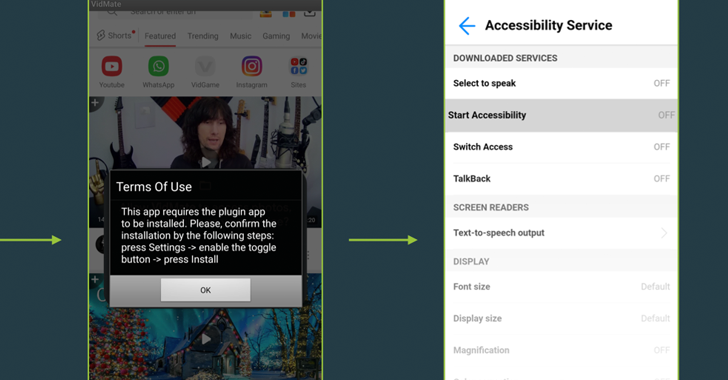
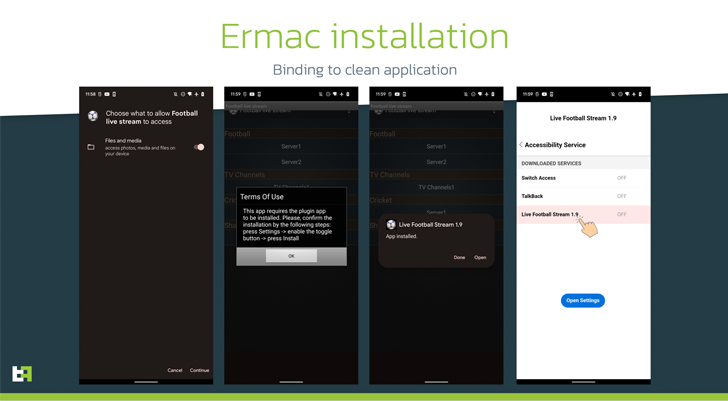
The ERMAC infections commence with a fraudulent website that claims to offer Wi-Fi authorization software for Android and Windows that, when installed, comes with features to steal seed phrases from crypto wallets and other sensitive data.
ThreatFabric said it also found a number of malicious apps that were trojanized versions of legitimate apps like Instagram, with the operators using them as droppers to deliver the obfuscated malicious payload.
The rogue apps, dubbed Zombinder, are said to have been developed using an APK binding service advertised on the dark web by a well-known threat actor since March 2022.
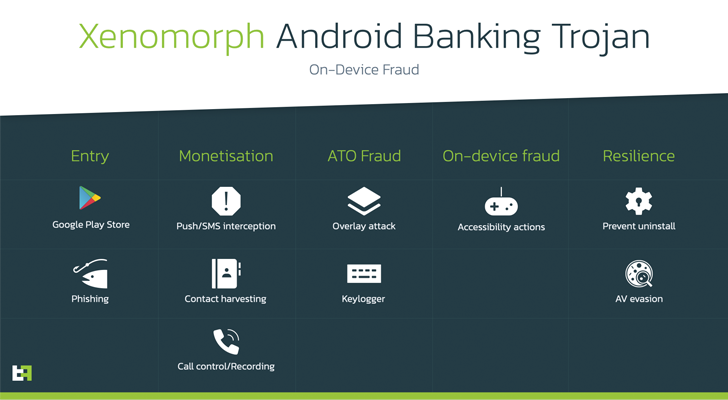
Such zombie apps have been used to distribute Android banking trojans like SOVA and Xenomorph targeting customers in Spain, Portugal, and Canada, among others.
Interestingly, the download option for Windows on the booby-trapped website distributing ERMAC is designed to deploy the Erbium and Aurora information stealers on the compromised system.
Erbium, which is a malware-as-a-service (MaaS) licensed for $1,000 per year, not only steals passwords and credit card information, but has also been observed acting as a conduit to drop the Laplas clipper that’s used to hijack crypto transactions.
“The presence of such a wide variety of trojans might also indicate that the malicious landing page is used by multiple actors and provided to them as a part of a third-party distribution service,” the researchers theorized.