ESET Research
ESET researchers discovered a zero-day Telegram for Android exploit that allows sending malicious files disguised as videos
22 Jul 2024
•
,
6 min. read
ESET researchers discovered a zero-day exploit that targets Telegram for Android, which appeared for sale for an unspecified price in an underground forum post from June 6th, 2024. Using the exploit to abuse a vulnerability that we named EvilVideo, attackers could share malicious Android payloads via Telegram channels, groups, and chat, and make them appear as multimedia files.
We were able to locate an example of the exploit, allowing us to analyze it further, and report it to Telegram on June 26th, 2024. On July 11th, they released an update that fixes the vulnerability in Telegram versions 10.14.5 and above.
Figure 1 is a video demonstration and explanation of the EvilVideo vulnerability.
Figure 1. Explanation of the EvilVideo vulnerability
Key points of the blogpost:
- On June 26th, 2024 in an underground forum, we found an advertisement for a zero-day exploit that targets Telegram for Android.
- We named the vulnerability it exploits EvilVideo and reported it to Telegram; their team patched it on July 11th, 2024.
- EvilVideo allows attackers to send malicious payloads that appear as video files in unpatched Telegram for Android.
- The exploit only works on Android Telegram versions 10.14.4 and older.
Discovery
We found the exploit being advertised for sale on an underground forum: see Figure 2.
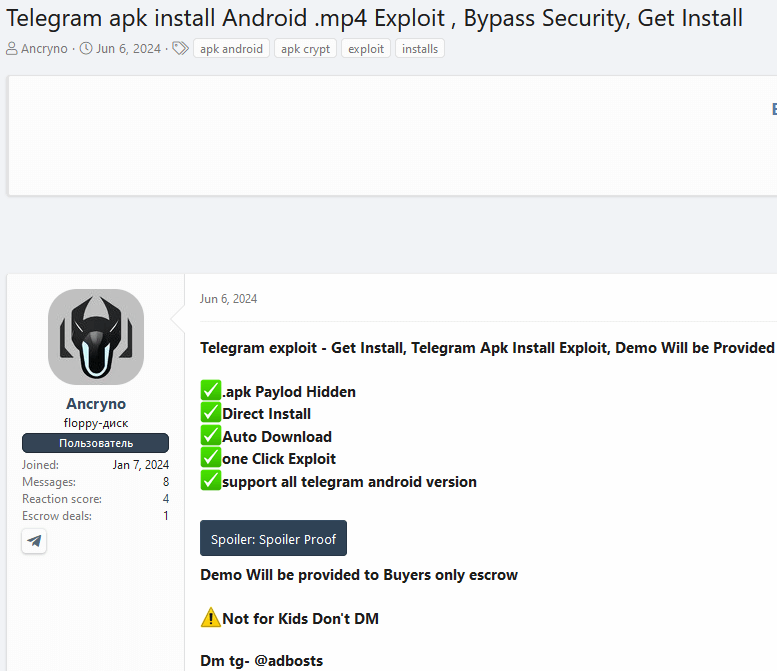
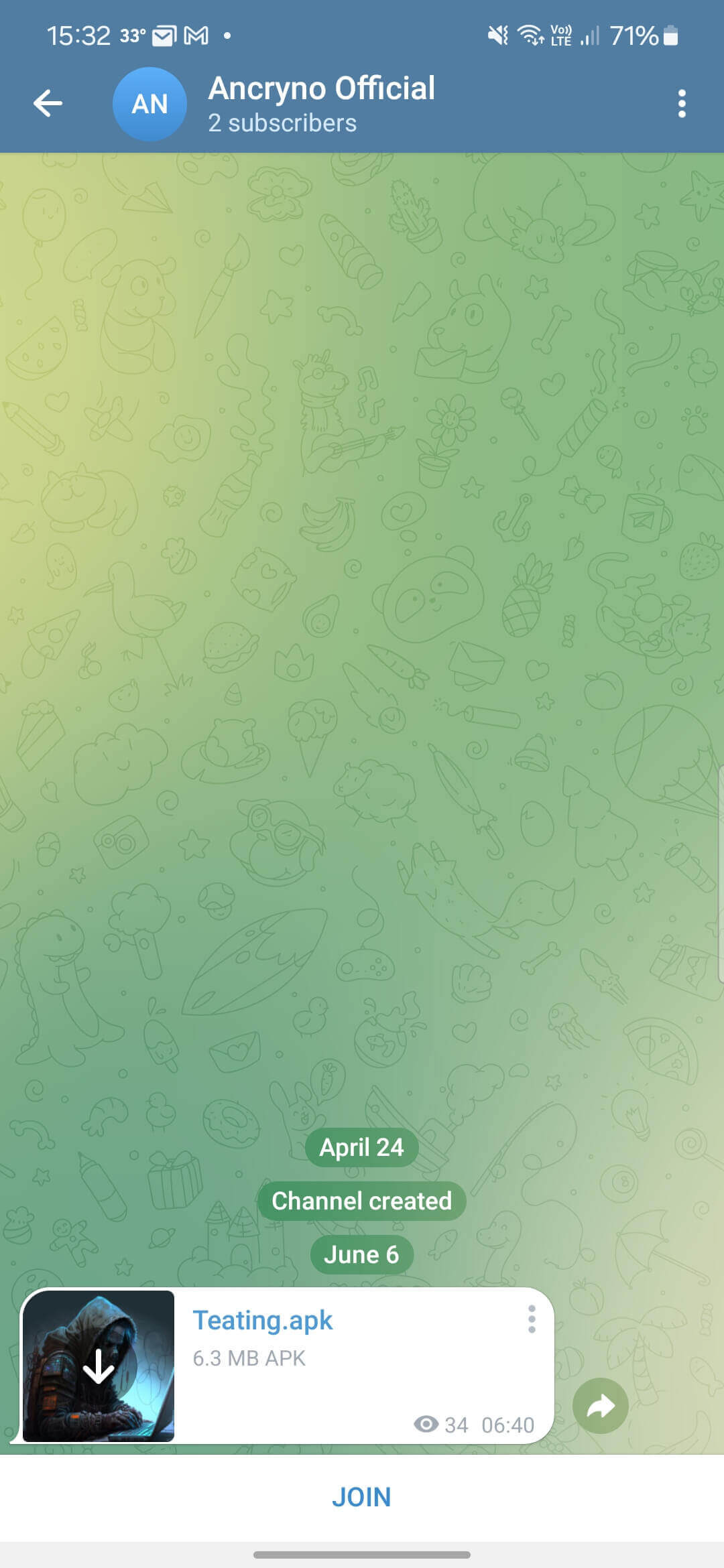
In the post, the seller shows screenshots and a video of testing the exploit in a public Telegram channel. We were able to identify the channel in question, with the exploit still available. That allowed us to get our hands on the payload and test it ourselves.
Analysis
Our analysis of the exploit revealed that it works on Telegram versions 10.14.4 and older. We speculate that the specific payload is most likely crafted using the Telegram API, since it allows developers to upload specifically crafted multimedia files to Telegram chats or channels programmatically.
The exploit seems to rely on the threat actor being able to create a payload that displays an Android app as a multimedia preview and not as a binary attachment. Once shared in chat, the malicious payload appears as a 30-second video (Figure 3).
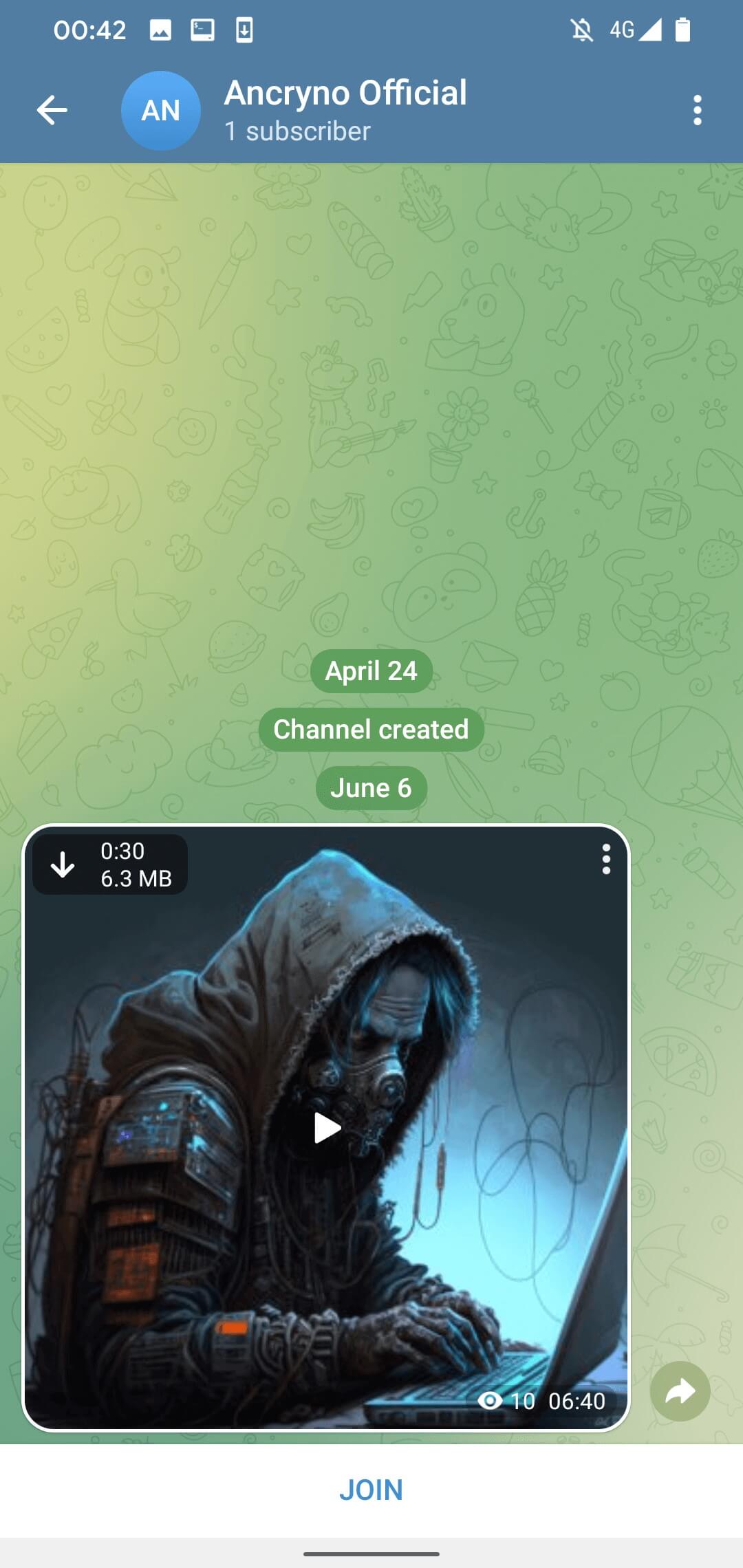
By default, media files received via Telegram are set to download automatically. This means that users with the option enabled will automatically download the malicious payload once they open the conversation where it was shared. The option can be disabled manually – in that case, the payload can still be downloaded by tapping the download button in the top left corner of the shared, apparent video, as is visible in Figure 3.
If the user tries to play the “video”, Telegram displays a message that it is unable to play it and suggests using an external player (see Figure 4). This is an original Telegram warning we found in the source code of the legitimate Telegram for Android app; it is not crafted and pushed by the malicious payload.
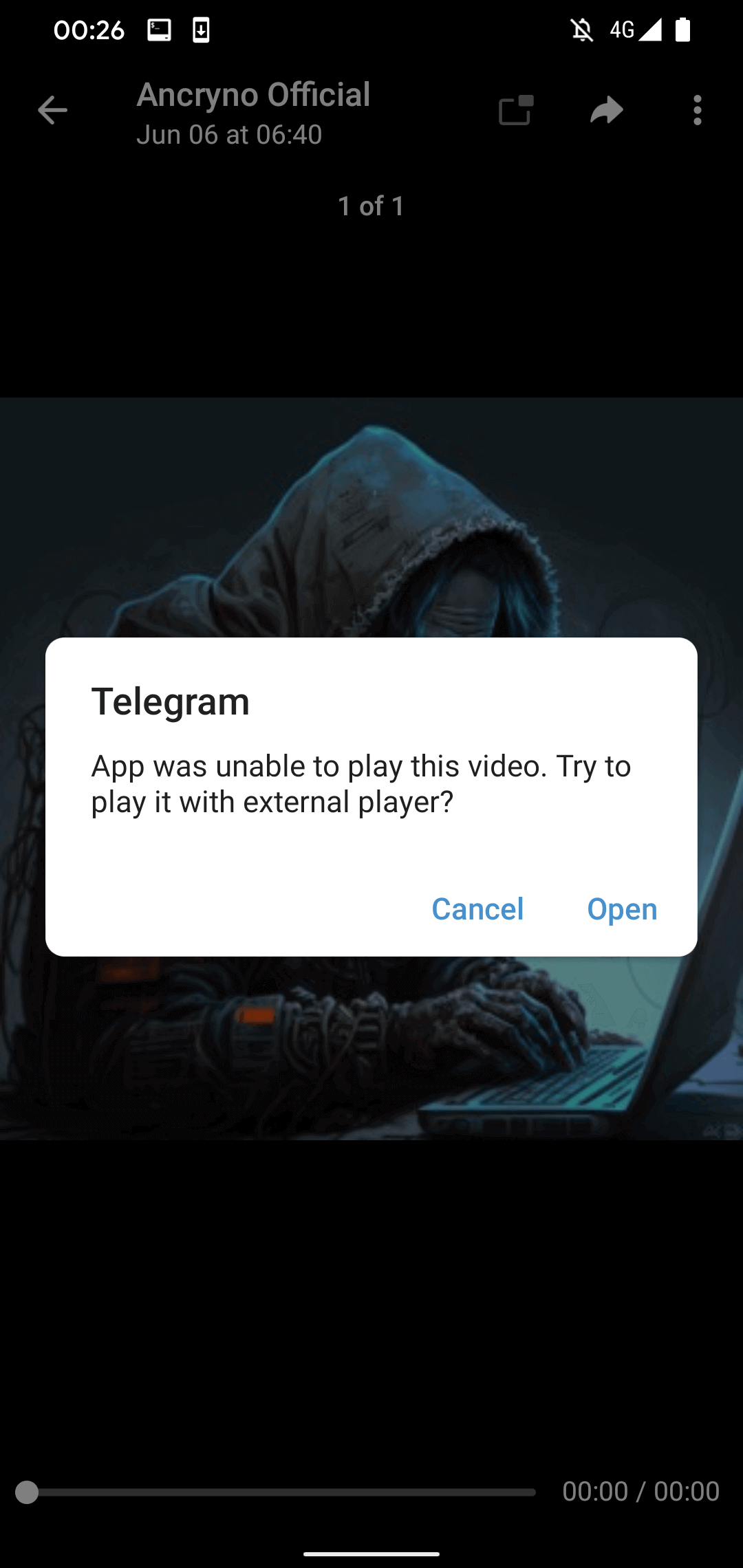
However, if the user taps the Open button in the displayed message, they will be requested to install a malicious app disguised as the aforementioned external player. As seen in Figure 5, before installation, Telegram will ask the user to enable the installation of unknown apps.
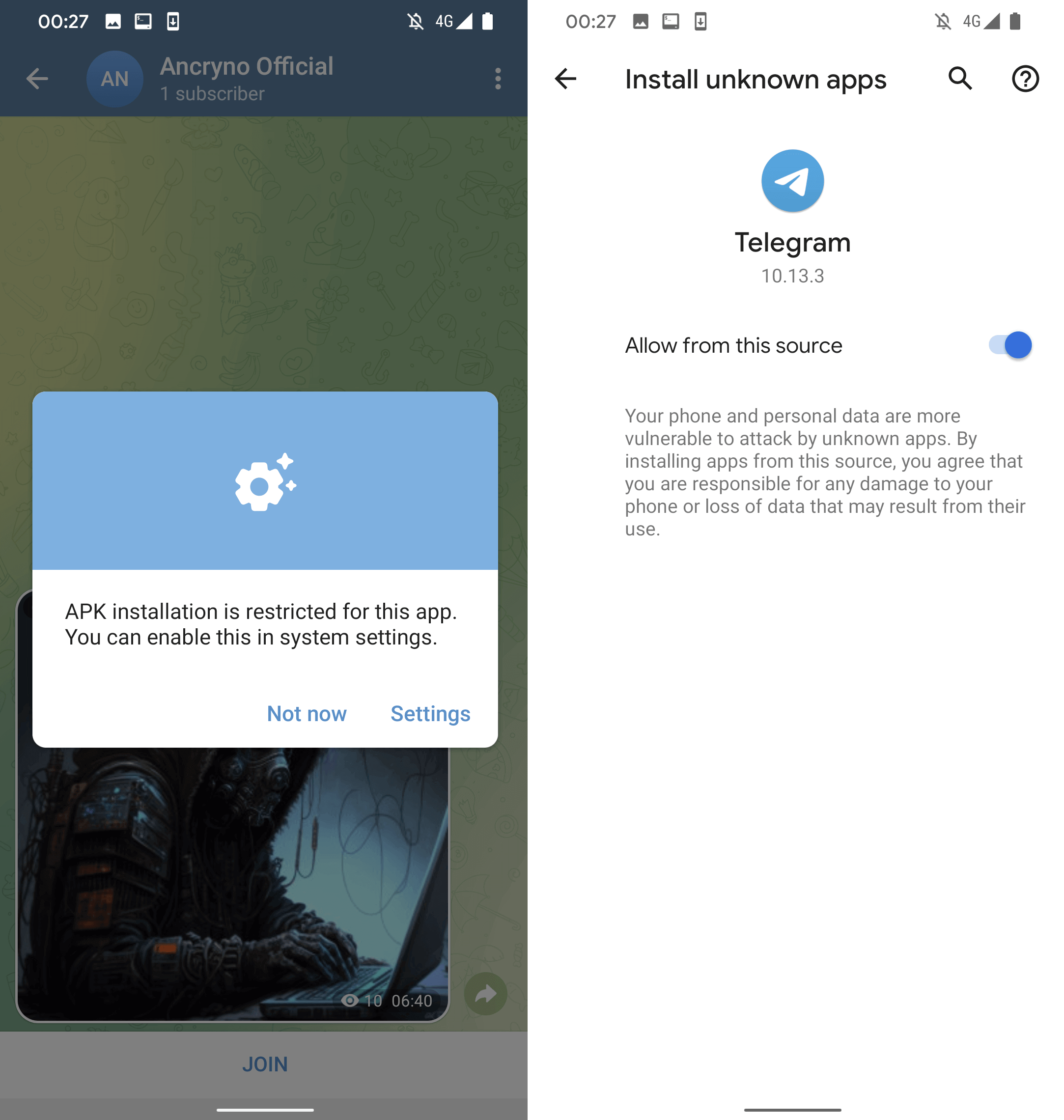
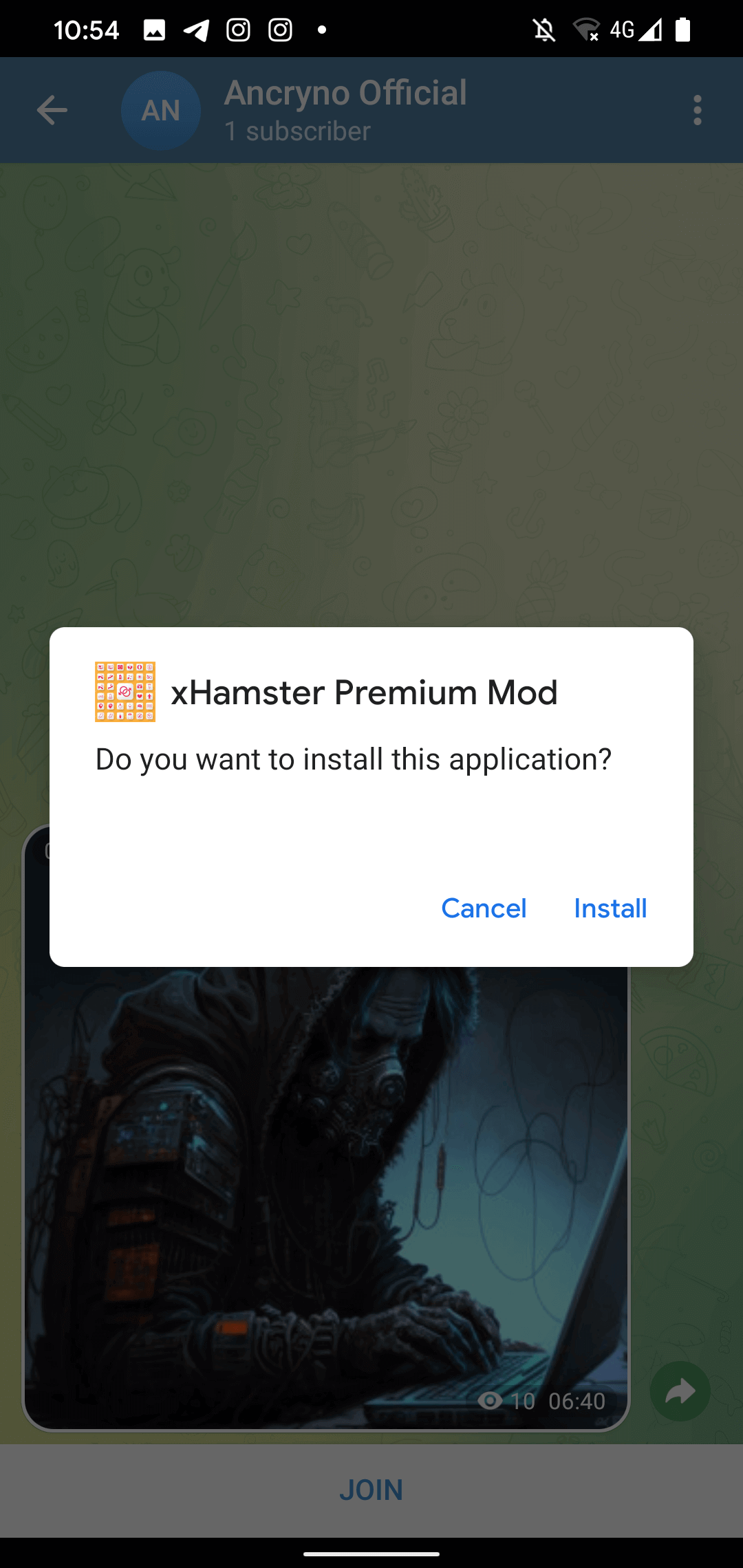
At this point, the malicious app in question has already been downloaded as the apparent video file, but with the .apk extension. Interestingly, it is the nature of the vulnerability that makes the shared file look like a video – the actual malicious app was not altered to pose as a multimedia file, which suggests that the upload process was most likely exploited. The malicious app’s installation request can be seen in Figure 6.
Unfortunately, we were unable to replicate the exploit, only inspect and verify the sample shared by the seller.
Telegram Web and Desktop
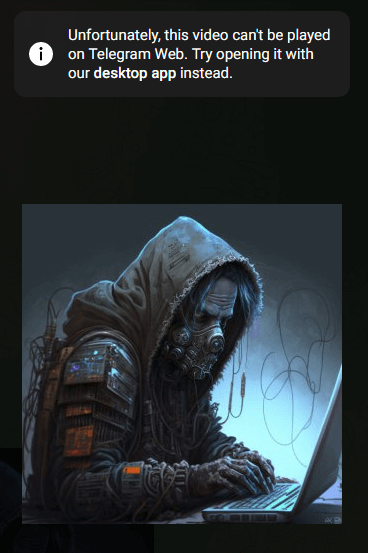
Even though the payload was made solely to target Telegram for Android, we still tried to test its behavior on other Telegram clients. We tested both the Telegram Web client and the Telegram Desktop client for Windows – as expected, the exploit did not work on either of them.
In the case of Telegram Web, after we tried playing the “video”, the client displayed an error message saying to try opening the video with the desktop app instead (see Figure 7). Downloading the attached file manually revealed its name and extension to be Teating.mp4. While the file itself was actually an Android executable binary (APK), Telegram treating it as an MP4 file stopped the exploit from working: in order for it to be successful, the attachment would have had to have the .apk extension.
A very similar thing happened with the Telegram Desktop client for Windows: the downloaded file was named Teating.apk.mp4, so it was once again an APK binary file with a .mp4 extension. This suggests that even if an attacker crafted a Windows executable to be used instead of the Android APK, it would still be treated as a multimedia file and the exploit would not work.
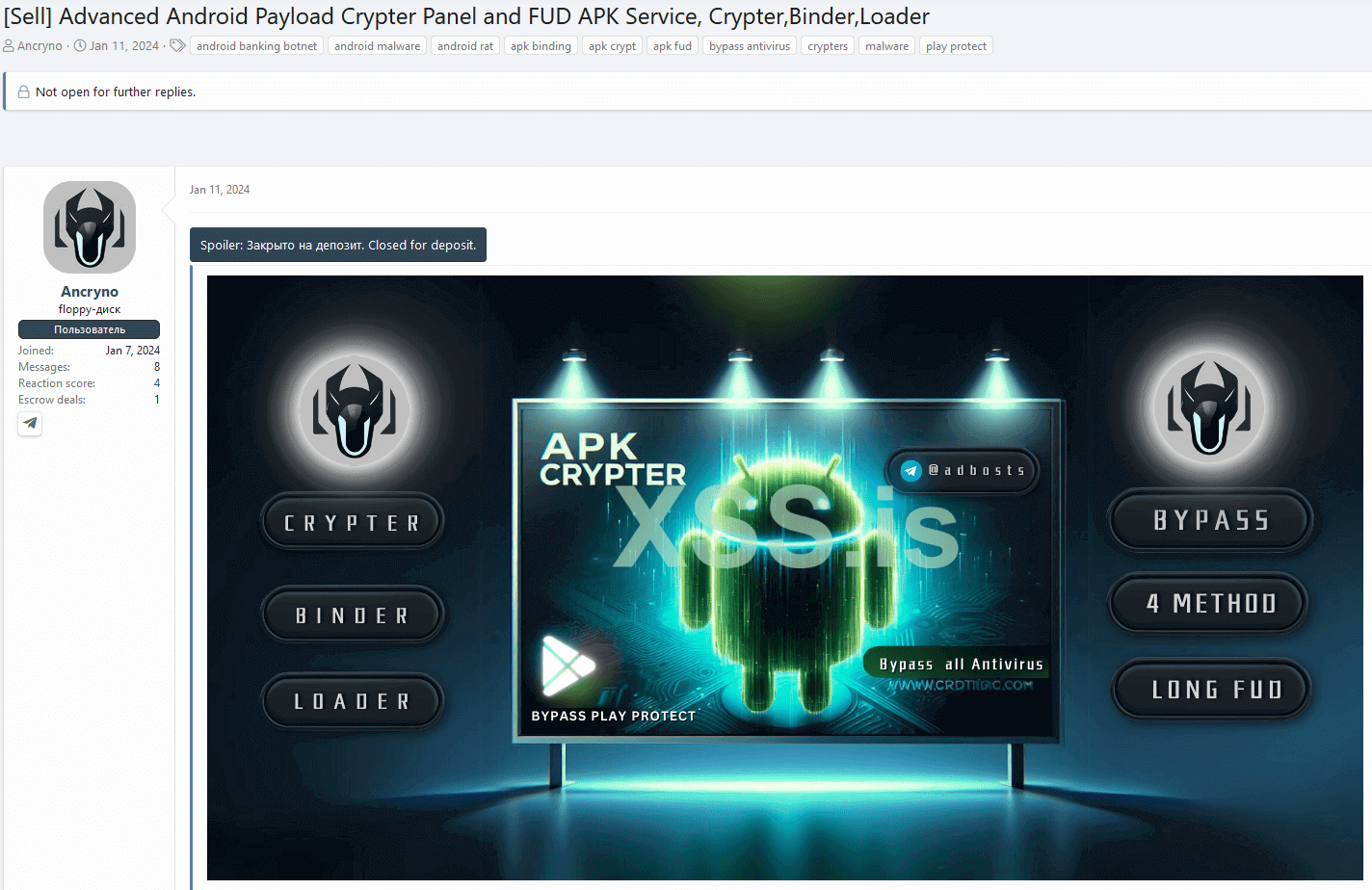
Threat actor
While we do not know much about the threat actor, we managed to find another shady service they are providing based on the Telegram handle the seller shared in their forum post. In addition to the exploit, they have been using the same underground forum to advertise an Android cryptor-as-a-service that they claim is fully undetectable (FUD) since January 11th, 2024. The forum post can be seen in Figure 8.
Vulnerability report
After discovering the EvilVideo vulnerability on June 26th, 2024, we followed our coordinated disclosure policy and reported it to Telegram, but received no response at the time. We reported the vulnerability again on July 4th, and that time, Telegram reached out to us the same day to confirm its team was investigating EvilVideo. They fixed the issue, shipping version 10.14.5 on July 11th, and informed us via email.
The vulnerability affected all versions of Telegram for Android up to 10.14.4, but has been patched as of version 10.14.5. As we verified, the chat multimedia preview now correctly displays that the shared file is an application (Figure 9) and not a video.
Conclusion
We discovered a zero-day Telegram for Android exploit for sale on an underground forum. The vulnerability it exploits allows sending malicious payloads that look like multimedia files via Telegram chat. If a user tries to play the apparent video, they will receive a request to install an external app, which actually installs the malicious payload. Luckily, the vulnerability has been fixed as of July 11th, 2024, after we reported it to Telegram.
For any inquiries about our research published on WeLiveSecurity, please contact us at threatintel@eset.comESET Research offers private APT intelligence reports and data feeds. For any inquiries about this service, visit the ESET Threat Intelligence page.
IoCs
A comprehensive list of Indicators of Compromise (IoCs) and samples can be found in our GitHub repository.
Files
|
SHA-1 |
Filename |
Detection |
Description |
|
F159886DCF9021F41EAA |
Teating.apk |
Android/Spy.SpyMax.T |
EvilVideo payload. |
Network
|
IP |
Domain |
Hosting provider |
First seen |
Details |
|
183.83.172[.]232 |
infinityhackscharan. |
Administrator Beam Cable System |
2024‑07‑16 |
C&C server of EvilVideo payload. |
MITRE ATT&CK techniques
This table was built using version 15 of the MITRE ATT&CK mobile techniques.
|
Tactic |
ID |
Name |
Description |
|
Initial Access |
Exploitation for Initial Access |
The EvilVideo vulnerability can be abused by Android malware to achieve initial device access. |
|
|
Execution |
Exploitation for Client Execution |
The EvilVideo vulnerability tricks the victim into installing a malicious app that impersonates a multimedia file. |


