In what’s the latest evolution of threat actors abusing legitimate infrastructure for nefarious ends, new findings show that nation-state hacking groups have entered the fray in leveraging the social platform for targeting critical infrastructure.
Discord, in recent years, has become a lucrative target, acting as a fertile ground for hosting malware using its content delivery network (CDN) as well as allowing information stealers to siphon sensitive data off the app and facilitating data exfiltration by means of webhooks.
“The usage of Discord is largely limited to information stealers and grabbers that anyone can buy or download from the Internet,” Trellix researchers Ernesto Fernández Provecho and David Pastor Sanz said in a Monday report.
But that may be changing, for the cybersecurity firm said it found evidence of an artifact targeting Ukrainian critical infrastructures. There is currently no evidence linking it to a known threat group.
“”The potential emergence of APT malware campaigns exploiting Discord’s functionalities introduces a new layer of complexity to the threat landscape,” the researchers noted.
The sample is a Microsoft OneNote file distributed via an email message impersonating the non-profit dobro.ua.
The file, once opened, contains references to Ukrainian soldiers to trick recipients into donating by clicking on a booby-trapped button, resulting in the execution of Visual Basic Script (VBS) designed to extract and run a PowerShell script in order to download another PowerShell script from a GitHub repository.
For its part, in the final stage, PowerShell takes advantage of a Discord webhook to exfiltrate system metadata.
“The fact that the only goal of the final payload is obtaining information about the system indicates that the campaign is still in an early stage, which also fits with the usage of Discord as [command-and-control],” the researchers said.
“However, it is important to highlight that the actor could deliver a more sophisticated piece of malware to the compromised systems in the future by modifying the file stored in the GitHub repository.”
Trellix’s analysis further revealed that loaders such as SmokeLoader, PrivateLoader, and GuLoader are among the most prevalent malware families that utilize Discord’s CDN to download a next-stage payload, including stealers like RedLine, Vidar, Agent Tesla, and Umbral.
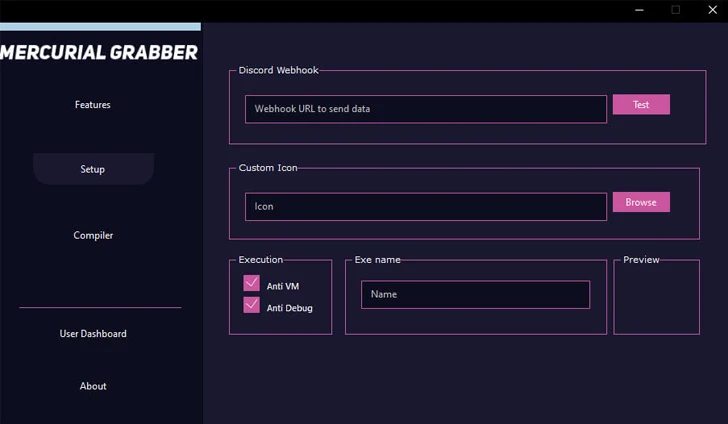
On top of that, some of the common malware families that have been observed using Discord webhooks are Mercurial Grabber, Stealerium, Typhon Stealer, and Venom RAT.
“The abuse of Discord’s CDN as a distribution mechanism for additional malware payloads showcases the adaptability of cybercriminals to exploit collaborative applications for their gain,” the researchers said.
“APTs are known for their sophisticated and targeted attacks, and by infiltrating widely used communication platforms like Discord, they can efficiently establish long-term footholds within networks, putting critical infrastructure and sensitive data at risk.”