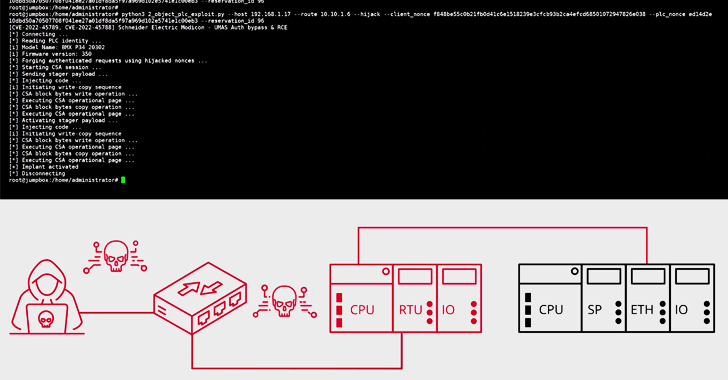
Security researchers have disclosed two new vulnerabilities affecting Schneider Electric Modicon programmable logic controllers (PLCs) that could allow for authentication bypass and remote code execution.
The flaws, tracked as CVE-2022-45788 (CVSS score: 7.5) and CVE-2022-45789 (CVSS score: 8.1), are part of a broader collection of security defects tracked by Forescout as OT:ICEFALL.
Successful exploitation of the bugs could enable an adversary to execute unauthorized code, denial-of-service, or disclosure of sensitive information.
The cybersecurity company said the shortcomings can be chained by a threat actor with known flaws from other vendors (e.g., CVE-2021-31886) to achieve deep lateral movement in operational technology (OT) networks.
“Deep lateral movement lets attackers gain deep access to industrial control systems and cross often overlooked security perimeters, allowing them to perform highly granular and stealthy manipulations as well as override functional and safety limitations,” Forescout said.
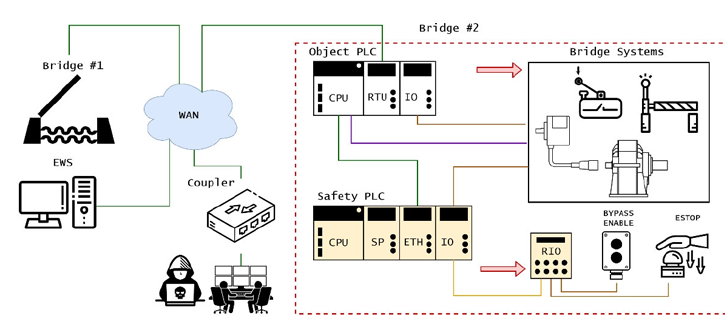
A highly intricate proof-of-concept (PoC) cyber-physical attack devised by the San Jose-based firm found that the flaws could be weaponized to bypass safety guardrails and inflict damage upon a movable bridge infrastructure.
With threat actors concocting sophisticated malware to disrupt industrial control systems, the deep lateral movement afforded by these flaws could permit adversaries to use an “uninteresting device as a staging point for moving towards more interesting targets.”
The findings come close on the heels of 38 security flaws that were revealed in wireless industrial internet of things (IIoT) devices and which could grant an attacker a direct line of access to OT networks, according to cybersecurity company Otorio.
Taken together, the weaknesses also underscore the real threats to physical operations from IoT devices, cloud-based management platforms, and nested OT networks.