A China-based financially motivated group is leveraging the trust associated with popular international brands to orchestrate a large-scale phishing campaign dating back as far as 2019.
The threat actor, dubbed Fangxiao by Cyjax, is said to have registered over 42,000 imposter domains, with initial activity observed in 2017.
“It targets businesses in multiple verticals including retail, banking, travel, and energy,” researchers Emily Dennison and Alana Witten said. “Promised financial or physical incentives are used to trick victims into further spreading the campaign via WhatsApp.”
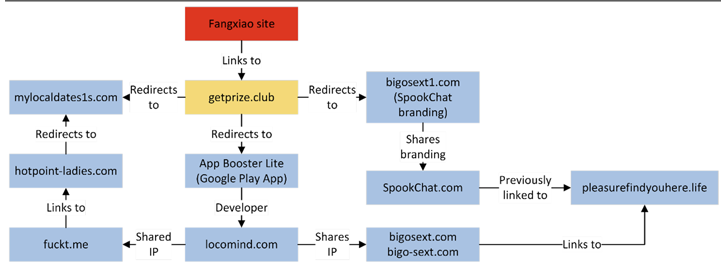
Users clicking on a link sent through the messaging app are directed to an actor-controlled site, which, in turn, sends them to a landing domain impersonating a well-known brand, from where the victims are once again taken to sites distributing fraudulent apps and bogus rewards.
These sites prompt the visitors to complete a survey to claim cash prizes, in exchange for which they are asked to forward the message to five groups or 20 friends. The final redirect, however, hinges on the IP address of the victim and the browser’s User-Agent string.
More than 400 organizations, including Emirates, Shopee, Unilever, Indomie, Coca-Cola, McDonald’s, and Knorr, are being imitated as part of the criminal scheme, the researchers said.
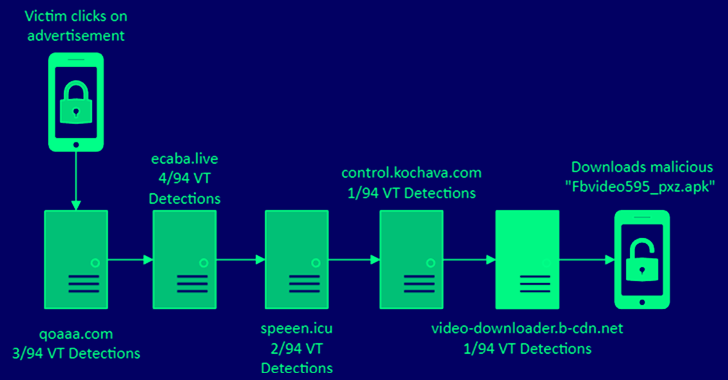
Alternatively, attacks wherein scammy mobile ads are clicked from an Android device have been observed to culminate in the deployment of a mobile trojan called Triada, which was recently spotted propagating via fake WhatsApp apps.
It’s not just Triada, as another destination of the campaign is the Google Play Store listing of an app called “App Booster Lite – RAM Booster” (com.app.booster.lite.phonecleaner.batterysaver.cleanmaster), which has over 10 million downloads.
The app, made by a Czechia-based developer known as LocoMind, is described as a “Powerful Phone Booster,” “Smart Junk Cleaner,” and an “Effective Battery Saver.”
Reviews for the app have called out the publisher for showing too many ads, and even point out that they “Arrived here [the Play Store page] from one of those ‘your android is damaged x%’ ads.”
“Our app can’t spread viruses,” LocoMind responded to the review on October 31, 2022. “Each of our updates is checked by Google Play – they would have removed our app long ago for this reason.”
Should the same action be performed from a device running iOS, the victim is redirected to Amazon via an affiliate link, netting the actor a commission for every purchase on the e-commerce platform made during the next 24 hours.
The threat actor’s China connections stem from the presence of Mandarin text in a web service associated with aaPanel, a Python-based open source control panel for hosting multiple websites.
Further analysis of the TLS certificates issued to the survey domains in 2021 and 2022 reveals that a bulk of the registrations overlap with the UTC+08:00 time zone, which corresponds to China Standard Time from 9:00 a.m. to 11:00 p.m.
“The operators are experienced in running these kinds of imposter campaigns, willing to be dynamic to achieve their objectives, and technically and logistically capable of scaling to expand their business,” the researchers said.
“The Fangxiao campaigns are effective lead generation methods which have been redirected to various domains, from malware, to referral links, to ads and adware.”