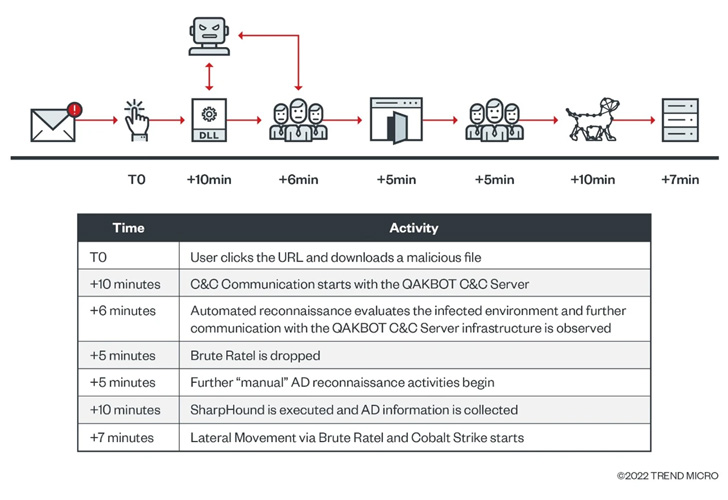
The threat actors behind the Black Basta ransomware family have been observed using the Qakbot trojan to deploy the Brute Ratel C4 framework as a second-stage payload in recent attacks.
The development marks the first time the nascent adversary simulation software is being delivered via a Qakbot infection, cybersecurity firm Trend Micro said in a technical analysis released last week.
The intrusion, achieved using a phishing email containing a weaponized link pointing to a ZIP archive, further entailed the use of Cobalt Strike for lateral movement.
While these legitimate utilities are designed for conducting penetration testing activities, their ability to offer remote access has made them a lucrative tool in the hands of attackers looking to stealthily probe the compromised environment without attracting attention for extended periods of time.
This has been compounded by the fact that a cracked version of Brute Ratel C4 began circulating last month across the cybercriminal underground, prompting its developer to update the licensing algorithm to make it harder to crack.
Qakbot, also called QBot and QuackBot, is an information stealer and banking trojan that’s known to be active since 2007. But its modular design and its ability to act as a downloader has turned it into an attractive candidate for dropping additional malware.
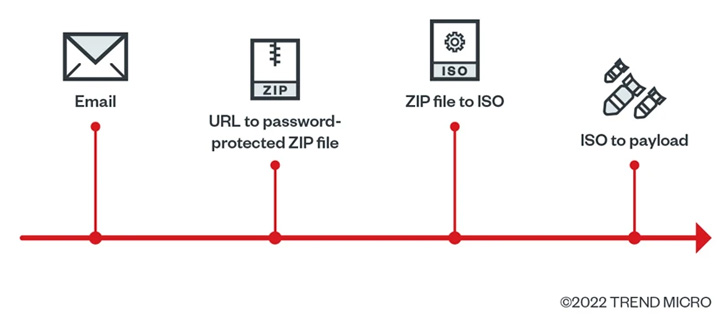
According to Trend Micro, the ZIP file in the email contains an ISO file, which, in turn, includes a LNK file that fetches the Qakbot payload, illustrating attempts on part of threat actors to adapt to other tactics in the aftermath of Microsoft’s decision to block macros by default for documents downloaded from the web.
The Qakbot infection is succeeded by the retrieval of Brute Ratel and Cobalt Strike, but not before performing automated reconnaissance through built-in command line tools such as arp, ipconfig, nslookup, netstat, and whoami.
The attack, however, was stopped before any malicious action could be taken by the threat actor, although it’s suspected that the end goal may have been domain-wide ransomware deployment.
In another Qakbot execution chain spotted by the cybersecurity company, the ZIP file is delivered through an increasingly popular method called HTML smuggling, resulting in the execution of Brute Ratel C4 as the second-stage.
“The Qakbot-to-Brute Ratel-to-Cobalt Strike kill chain is associated with the group behind the Black Basta Ransomware,” the researchers said. “This is based on overlapping TTPs and infrastructure observed in Black Basta attacks.”
The findings coincide with a resurgence of Qakbot attacks in recent months by means of a variety of techniques like HTML file attachments, DLL side-loading, and email thread hijacking, the last of which entailed harvesting emails in bulk from successful ProxyLogon attacks aimed at Microsoft Exchange servers.
IcedID Actors Diversify Delivery Methods
Qakbot is far from the only access-as-a-service malware that’s being increasingly distributed via ISO and other file formats to get around macro restrictions, for Emotet, IcedID, and Bumblebee campaigns have all followed similar trajectories.
Palo Alto Networks Unit 42, in late September 2022, said it discovered a malicious polyglot Microsoft Compiled HTML Help (CHM) file being used to deliver the IcedID (aka BokBot) malware.
Other prominent delivery methods and infection pathways have involved the use of password-protected ZIP files containing an ISO file, mirroring that of Qakbot, with the payload propagated through a pay-per-installer service known as PrivateLoader, according to Team Cymru.
And, to top it all, Emotet appears to be readying for a fresh set of attacks after a short three-month hiatus to rework its “systeminfo” module to “improve targeting of specific victims and distinguish tracking bots from real users,” ESET disclosed in a series of tweets.
“We have not seen new spam waves from Emotet since July,” Jean-Ian Boutin, director of threat research at ESET, told The Hacker News. “It is not clear why that is.”
“They did take some breaks in the past, but never for that long. Perhaps this new module means that they are testing modules and will be active again in the near future, but this of course is speculation.”