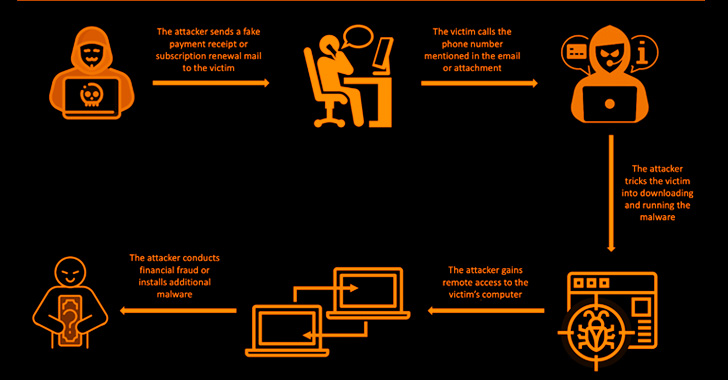
The operators behind the BazaCall call back phishing method have continued to evolve with updated social engineering tactics to deploy malware on targeted networks.
The scheme eventually acts as an entry point to conduct financial fraud or the delivery of next-stage payloads such as ransomware, cybersecurity company Trellix said in a report published last week.
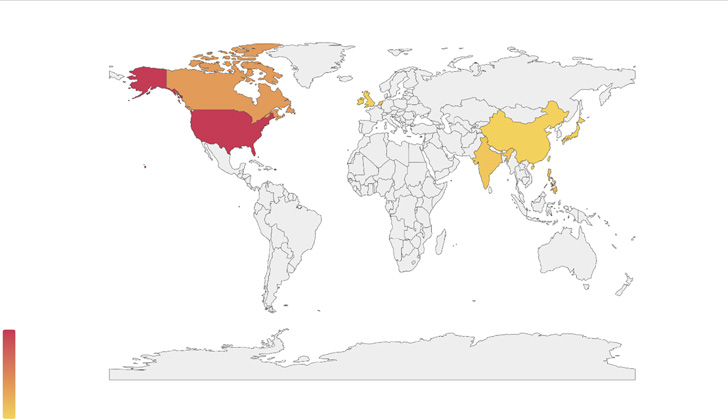
Primary targets of the latest attack waves include the U.S., Canada, China, India, Japan, Taiwan, the Philippines, and the U.K.
BazaCall, also called BazarCall, first gained popularity in 2020 for its novel approach of distributing the BazarBackdoor (aka BazarLoader) malware by manipulating potential victims into calling a phone number specified in decoy email messages.
These email baits aim to create a false sense of urgency, informing the recipients about renewal of a trial subscription for, say, an antivirus service. The messages also urge them to contact their support desk to cancel the plan, or risk getting automatically charged for the premium version of the software.
The ultimate goal of the attacks is to enable remote access to the endpoint under the guise of terminating the supposed subscription or installing a security solution to rid the machine of malware, effectively paving the way for follow-on activities.
Another tactic embraced by the operators involves masquerading as incident responders in PayPal-themed campaigns to deceive the caller into thinking that their accounts were accessed from eight or more devices spread across random locations across the world.
Regardless of the scenario employed, the victim is prompted to launch a specific URL – a specially crafted website designed to download and execute a malicious executable that, among other files, also drops the legitimate ScreenConnect remote desktop software.
A successful persistent access is followed by the attacker opening fake cancellation forms that ask the victims to fill out personal details and sign in to their bank accounts to complete the refund, but in reality are fooled into sending the money to the scammer.
The development comes as at least three different spinoff groups from the Conti ransomware cartel have embraced the call back phishing technique as an initial intrusion vector to breach enterprise networks.
The ties to Conti don’t end there. BazarBackdoor, for its part, is the creation of a cybercrime group known as TrickBot, which was taken over by Conti earlier this year before the latter’s shutdown in May-June 2022 over its allegiance to Russia in its assault on Ukraine.