The threat actors behind a large-scale adversary-in-the-middle (AiTM) phishing campaign targeting enterprise users of Microsoft email services have also set their sights on Google Workspace users.
“This campaign specifically targeted chief executives and other senior members of various organizations which use [Google Workspace],” Zscaler researchers Sudeep Singh and Jagadeeswar Ramanukolanu detailed in a report published this month.
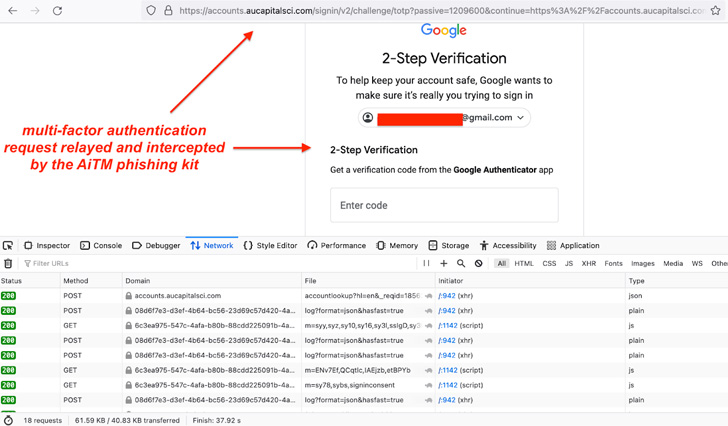
The AitM phishing attacks are said to have commenced in mid-July 2022, following a similar modus operandi as that of a social engineering campaign designed to siphon users’ Microsoft credentials and even bypass multi-factor authentication.
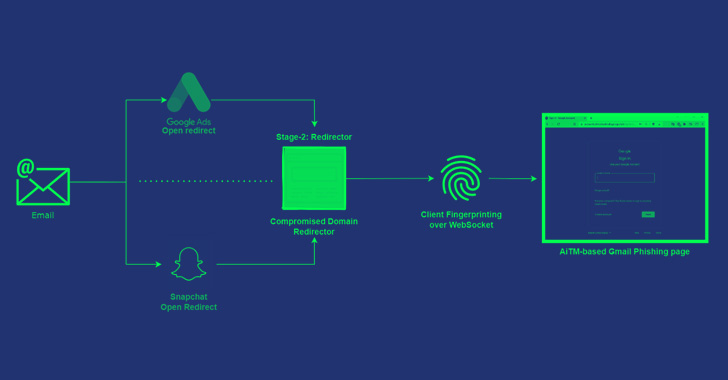
The low-volume Gmail AiTM phishing campaign also entails using the compromised emails of chief executives to conduct further phishing attacks by the threat actor, with the attacks also utilizing several compromised domains as an intermediate URL redirector to take the victims to the landing page.
Attack chains involve sending password expiry emails to potential targets that contain an embedded malicious link to supposedly “extend your access,” tapping which takes the recipient to open redirect pages of Google Ads and Snapchat to load the phishing page URL.
Beside open redirect abuse, a second variant of the attacks relies on infected sites which host a Base64-encoded version of the next-stage redirector and the victim’s email address in the URL. This intermediate redirector is a JavaScript code that points to a Gmail phishing page.
In one instance highlighted by Zscaler, the redirector page used in the Microsoft AiTM phishing attack on July 11, 2022, was updated to take the user to a Gmail AiTM phishing page, connecting the two campaigns to the same threat actor.
“There was also an overlap of infrastructure, and we even identified several cases in which the threat actor switched from Microsoft AiTM phishing to Gmail phishing using the same infrastructure,” the researchers said.
The findings are an indication that multi-factor authentication safeguards alone cannot offer protections against advanced phishing attacks, necessitating that users scrutinize URLs before entering credentials and refrain from opening attachments or clicking on links in emails sent from untrusted or unknown sources.