Researchers have disclosed multiple vulnerabilities impacting Ultra-wideband (UWB) Real-time Locating Systems (RTLS), enabling threat actors to launch adversary-in-the-middle (AitM) attacks and tamper with location data.
“The zero-days found specifically pose a security risk for workers in industrial environments,” cybersecurity firm Nozomi Networks disclosed in a technical write-up last week. “If a threat actor exploits these vulnerabilities, they have the ability to tamper with safety zones designated by RTLS to protect workers in hazardous areas.”
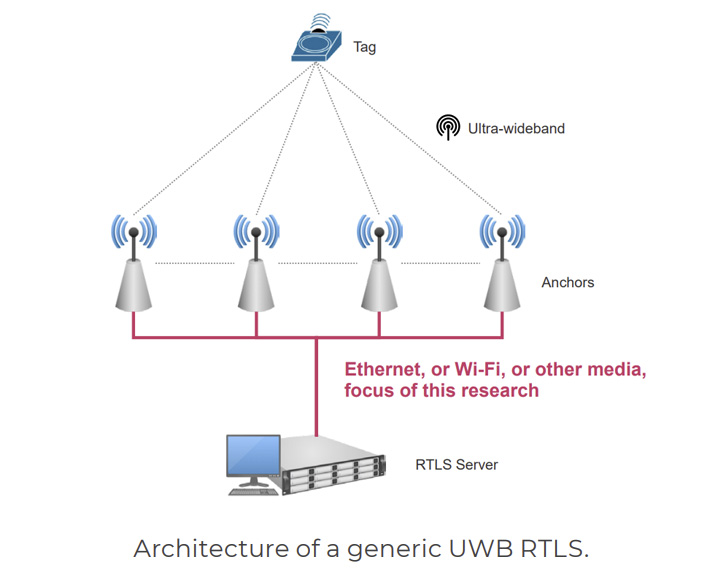
RTLS is used to automatically identify and track the location of objects or people in real-time, usually within a confined indoor area. This is achieved by making use of tags that are attached to assets, which broadcast USB signals to fixed reference points called anchors that then determine their location.
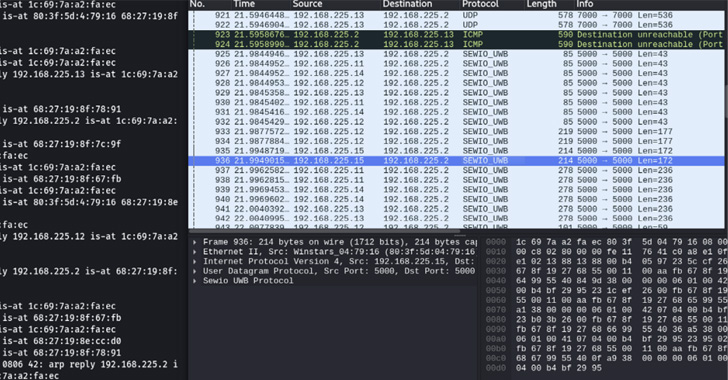
But flaws identified in RTLS solutions – Sewio Indoor Tracking RTLS UWB Wi-Fi Kita and Avalue Renity Artemis Enterprise Kit – meant that they could be weaponized to intercept network packets exchanged between anchors and the central server and stage traffic manipulation attacks.
Put simply, the idea is to estimate the anchor coordinates and use it to manipulate the geofencing rules of the RTLS system, effectively tricking the software into granting access to restricted areas and even causing disruption to production environments.
“If an attacker is able to alter the position of a tag by modifying the positioning packet related to that tag, it may become possible to enter restricted zones or steal valuable items without the operators being able to detect that a malicious activity is ongoing.”
Even worse, by altering the position of tags and placing them inside areas monitored by geofencing rules, an adversary can cause the stoppage of entire production lines by showing that a worker is nearby even when no one is actually around.
In an alternate scenario, the location data could be tampered to place a worker outside of a geofencing zone so that dangerous machinery would restart while a worker is in close proximity, posing severe safety risks.
But it’s worth pointing out that doing so necessitates that an attacker either compromises a computer connected to that network, or surreptitiously adds a rogue device to gain unauthorized access to the network.
To remediate such attacks, it’s recommended to enforce network segregation and add a traffic encryption layer on top of the existing communications to prevent AitM attacks.
“Weak security requirements in critical software can lead to safety issues that cannot be ignored,” researchers Andrea Palanca, Luca Cremona, and Roya Gordon said. “Exploiting secondary communications in UWB RTLS can be challenging, but it is doable.”