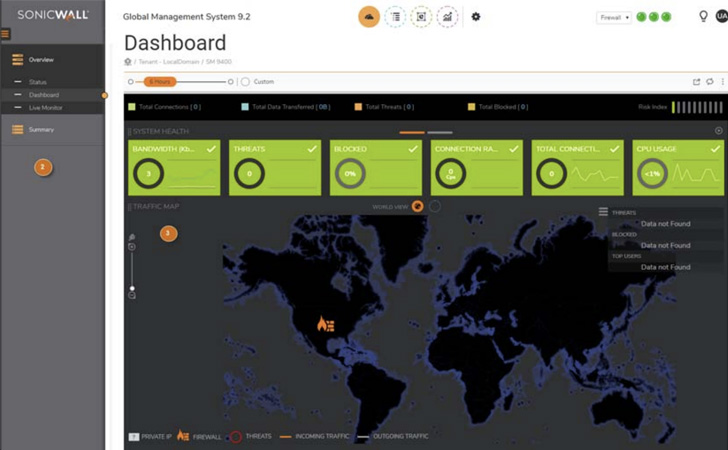
Network security company SonicWall on Friday rolled out fixes to mitigate a critical SQL injection (SQLi) vulnerability affecting its Analytics On-Prem and Global Management System (GMS) products.
The vulnerability, tracked as CVE-2022-22280, is rated 9.4 for severity on the CVSS scoring system and stems from what the company describes is an “improper neutralization of special elements” used in an SQL command that could lead to an unauthenticated SQL injection.
“Without sufficient removal or quoting of SQL syntax in user-controllable inputs, the generated SQL query can cause those inputs to be interpreted as SQL instead of ordinary user data,” MITRE notes in its description of SQL injection.
“This can be used to alter query logic to bypass security checks, or to insert additional statements that modify the back-end database, possibly including execution of system commands.”
H4lo and Catalpa of DBappSecurity HAT Lab have been credited with discovering and reporting the flaws which affect 2.5.0.3-2520 and earlier versions of Analytics On-Prem as well as all versions of GMS prior to and including 9.3.1-SP2-Hotfix1.
Organizations relying on vulnerable appliances are recommended to upgrade to Analytics 2.5.0.3-2520-Hotfix1 and GMS 9.3.1-SP2-Hotfix-2.
“There is no workaround available for this vulnerability,” SonicWall said. “However, the likelihood of exploitation may be significantly reduced by incorporating a Web Application Firewall (WAF) to block SQLi attempts.”