LockBit ransomware attacks are constantly evolving by making use of a wide range of techniques to infect targets while also taking steps to disable endpoint security solutions.
“The affiliates that use LockBit’s services conduct their attacks according to their preference and use different tools and techniques to achieve their goal,” Cybereason security analysts Loïc Castel and Gal Romano said. “As the attack progresses further along the kill chain, the activities from different cases tend to converge to similar activities.”
LockBit, which operates on a ransomware-as-a-service (RaaS) model like most groups, was first observed in September 2019 and has since emerged as the most dominant ransomware strain this year, surpassing other well-known groups like Conti, Hive, and BlackCat.
This involves the malware authors licensing access to affiliates, who execute the attacks in exchange for using their tools and infrastructure and earn as much as 80% of each successful ransom payment received from the victims.
LockBit also utilizes the popular technique of double extortion to exfiltrate vast amounts of data prior to encrypting the assets of the target, netting the cybercriminal syndicate no fewer than 850 victims on its data leak site as of May 2022.
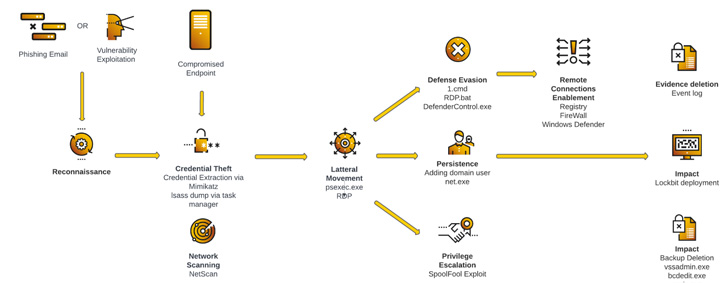 |
| Attack Life Cycle – Case Study 1 |
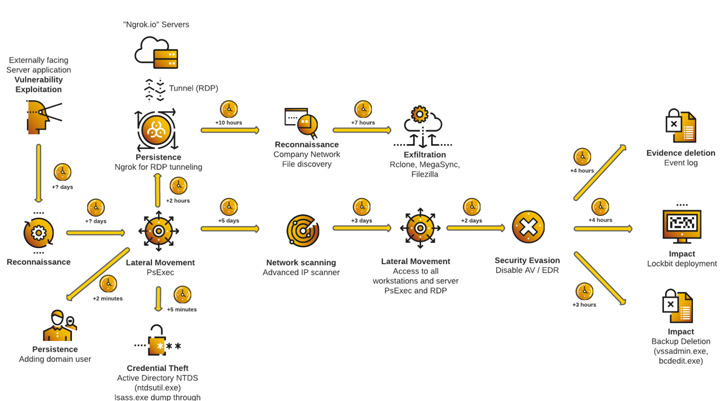 |
| Attack Life Cycle – Case Study 2 |
According to a leak site data analysis by Palo Alto Networks Unit 42, LockBit accounted for 46% of all ransomware-related breach events for the first quarter of 2022. In June alone, the group has been tied to 44 attacks, making it the most active ransomware strain.
LockBit ransomware attacks are known to employ several avenues for initial infection: Exploiting publicly-exposed RDP ports, relying on phishing emails to download malicious payloads, or leveraging unpatched server flaws that allow the affiliates to gain remote access to the targeted network.
Following this step are reconnaissance and credential theft activities, which enable the actors to move laterally across the network, establish persistence, escalate privileges, and launch the ransomware. This is also accompanied by running commands to delete backups and subvert detection by firewalls and antivirus software.
In the three years since LockBit appeared on the scene, the RaaS scheme has received two notable upgrades, with the threat actors debuting LockBit 2.0 in June 2021 and launching the third installment of the service, LockBit 3.0, last month with support for Zcash cryptocurrency payment options and a bug bounty program — the first for a ransomware group.
The initiative claims to offer rewards of up to $1 million for finding security blind spots in its website and locker software, submitting brilliant ideas, doxing the head of the gang’s affiliate program, or identifying ways that could expose the IP of the server hosting the website on the TOR network.
The bug bounty program is yet another sign that hacker groups are increasingly functioning as legitimate IT enterprises, incorporating HR departments, regular feature releases, and even bonuses for solving challenging problems.
However, indications are that LockBit 3.0, also called LockBit Black, is inspired by another ransomware family known as BlackMatter, a rebranded version of DarkSide that shuttered in November 2021.
“Large portions of the code are ripped straight from BlackMatter/Darkside,” Emsisoft researcher Fabian Wosar said in a tweet earlier this week. “Guess it is clear that LockBit got their dirty hands on another group’s code.”