Authored by Oliver Devane and Vallabh Chole
Notifications on Chrome and Edge, both desktop browsers, are commonplace, and malicious actors are increasingly abusing this feature. McAfee previously blogged about how to change desktop browser settings to stop malicious notifications. This blog focuses on Chrome notifications on Android mobile devices such as phones and tablets, and how McAfee Mobile Security protects users from malicious sites leveraging these notifications.
Where do these notifications come from?
Most users are unaware of the source of these notifications. Permission is granted when a user clicks ‘Allow’ on a prompt within Android Chrome.
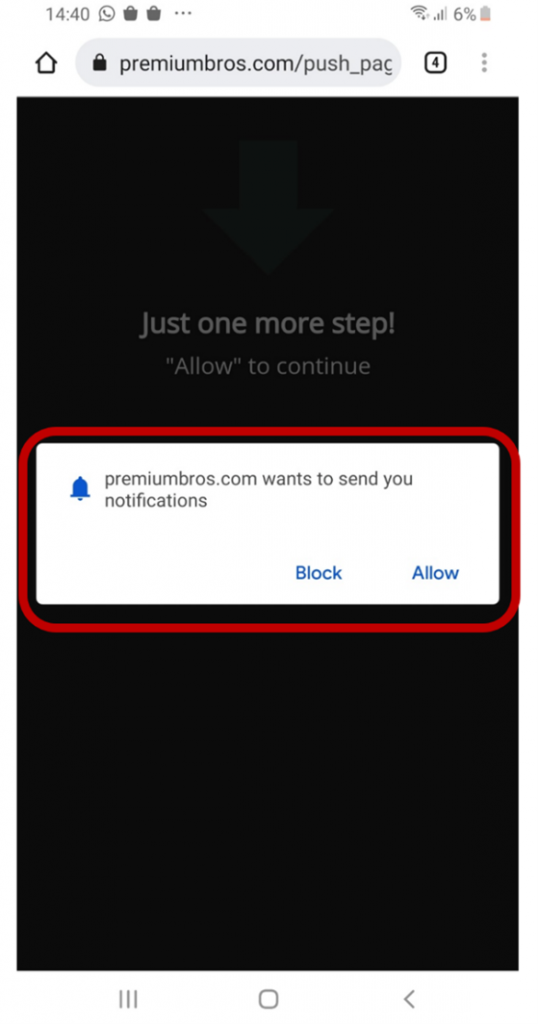
Many malicious websites use language and images like the one above that entice the user to click ‘Allow’ such as ‘Just one more step! Click “Allow” to continue. Once allow is clicked, the website is added to a site permissions list, which will enable it to send notifications.
What do they look like?
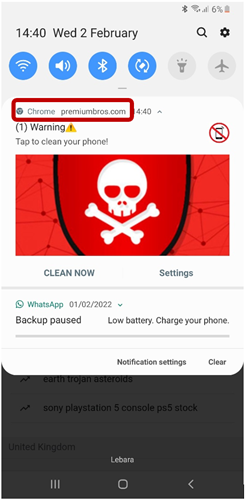
The notifications will look like a usual Android notification which you will be used to seeing such as you have a new WhatsApp message or email. To identify the source of the notification, we need to look for the application name which is like the one highlighted in the red box below.
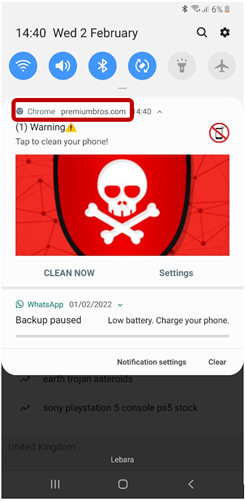
The image above shows the notification came from Chrome and it is from the website premiumbros[.]com. This is something you should pay attention to as it will be needed when you want to stop annoying notifications.
How are some they malicious?
Some notifications like the ones in this blog are malicious as they attempt to trick users into believing that their mobile device is infected with a virus and some action is required. When the users click the notification, Chrome will load a website which will present them with a fake warning like the example below:
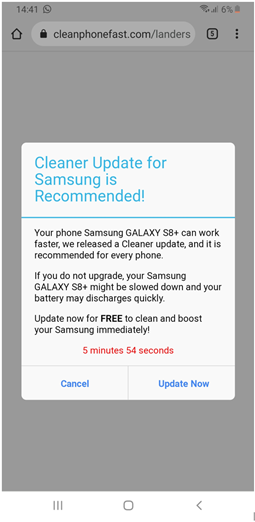
Clicking either Cancel or Update Now on the above website will result in the same behavior. The browser will redirect the user to a google play store app so that they can download and install it.
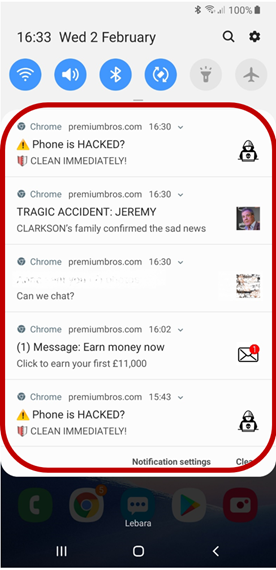
The malicious websites will flood your phone with several notifications. The screenshot below shows an example of this:
Why do malicious actors do this?
You may ask yourself, why do malicious actors try to get me to install a google play application? The people behind these scams receive a commission when these applications are installed on devices. They rely on deceptive tactics to trick users into installing them to maximize profits.
How can I remove notifications?
To remove a website’s notification permission, you need to change a Chrome setting.
1- Find out the name of the website which is sending these notifications. This can be done by looking at the notification and noting down the name of the website. If we use this blog as an example, it would be premiumbros[.]com
2- Open the Chrome browser app which can be found by performing the following search:
![]()
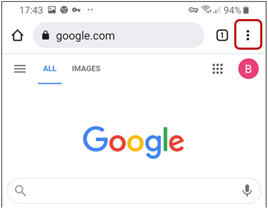
3- Click the three … on the top right hand of the application
4- Scroll down and click on settings
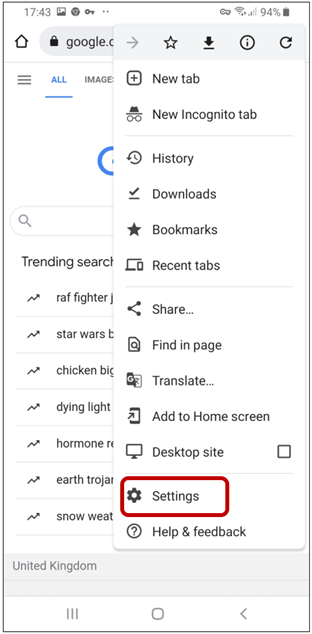
5- Click on Notifications
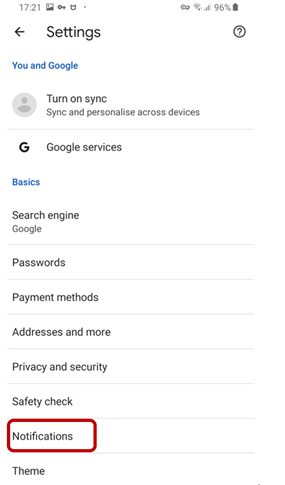
6- Scroll down until you find the website which you identified in step 1
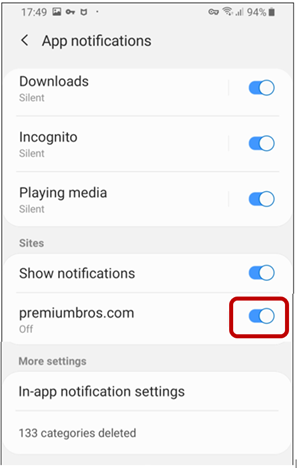
7- Pres the blue radio button so it turns grey
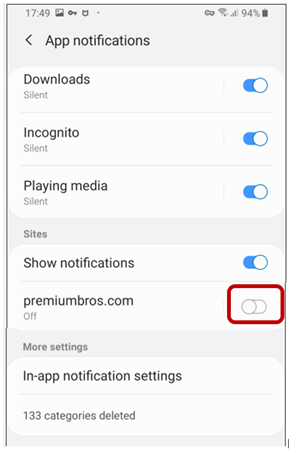
8- Notifications will now be disabled for that website. If you want to block multiple websites, click the radio button for them as well.
How does McAfee Protect me?
McAfee customers who have McAfee Mobile Security are protected against these malicious websites as long as they enable the ‘Safe Browsing’ feature within the application.
Upon trying to access a malicious website such as the one in the blog it will be blocked as shown in the image below:
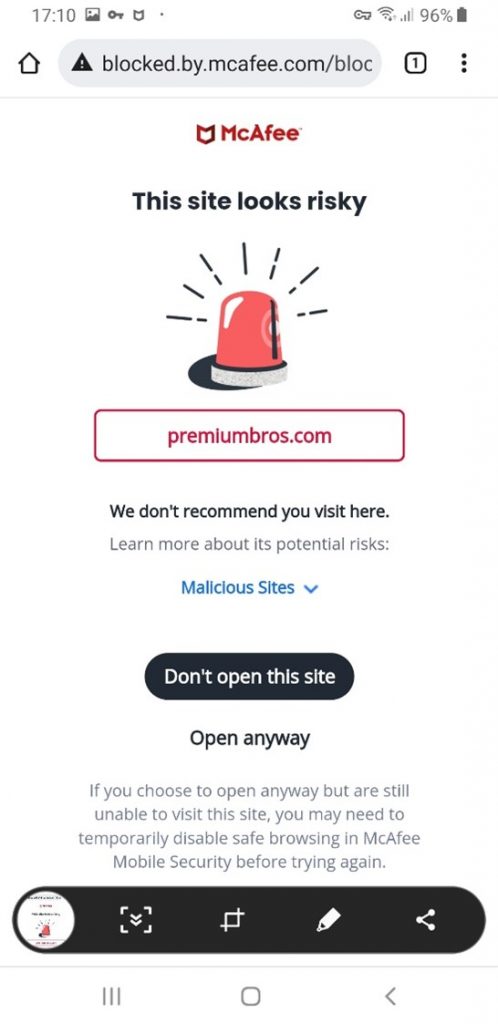
Please read this guide on enabling the Safe Browsing feature within the Mobile Security Application.
