A targeted phishing campaign aimed at the aviation industry for two years may be spearheaded by a threat actor operating out of Nigeria, highlighting how attackers can carry out small-scale cyber offensives for extended periods of time while staying under the radar.
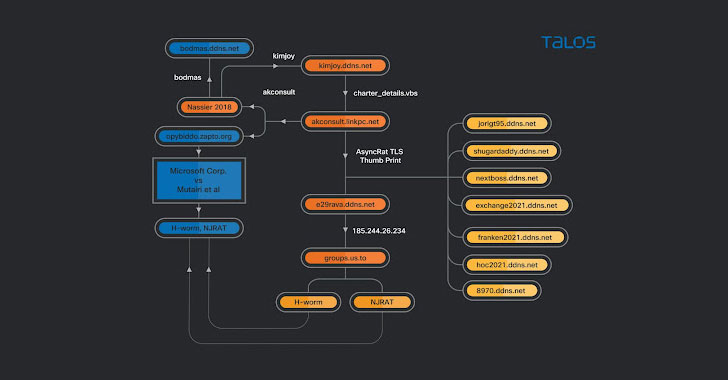
Cisco Talos dubbed the malware attacks “Operation Layover,” building on previous research from the Microsoft Security Intelligence team in May 2021 that delved into a “dynamic campaign targeting the aerospace and travel sectors with spear-phishing emails that distribute an actively developed loader, which then delivers RevengeRAT or AsyncRAT.”
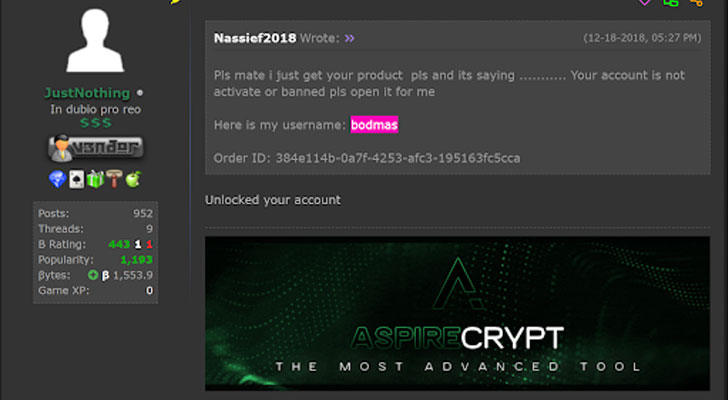
“The actor […] doesn’t seem to be technically sophisticated, using off-the-shelf malware since the beginning of its activities without developing its own malware,” researchers Tiago Pereira and Vitor Ventura said. “The actor also buys the crypters that allow the usage of such malware without being detected, throughout the years it has used several different cryptors, mostly bought on online forums.”
The threat actor is believed to have been active at least since 2013. The attacks involve emails containing specific lure documents centered around the aviation or cargo industry that purport to be PDF files but link to a VBScript file hosted on Google Drive, which ultimately leads to the delivery of remote access trojans (RATs) like AsyncRAT and njRAT, leaving organizations vulnerable to an array of security risks. Cisco Talos said it found 31 different aviation-themed lures dating all the way back to August 2018.
Further analysis of the activity associated with different domains used in the attacks show that the actor weaved multiple RATs into their campaigns, with the infrastructure used as command-and-control (C2) servers for Cybergate RAT, AsyncRAT, and a batch file that’s used as part of a malware chain to download and execute other malware.
“Many actors can have limited technical knowledge but still be able to operate RATs or information-stealers, posing a significant risk to large corporations given the right conditions,” the researchers said. “In this case, […] what seemed like a simple campaign is, in fact, a continuous operation that has been active for three years, targeting an entire industry with off-the-shelf malware disguised with different crypters.”